Cybersecurity researchers have disclosed multiple security flaws in video surveillance products from Axis Communications that, if successfully exploited, could expose them to takeover attacks.
“The attack results in pre-authentication remote code execution on Axis Device Manager, a server used to configure and manage fleets of cameras, and the Axis Camera Station, client software used to view camera feeds,” Claroty researcher Noam Moshe said.
“Furthermore, using internet scans of exposed Axis.Remoting services, an attacker can enumerate vulnerable servers and clients, and carry out granular, highly targeted attacks.”

The list of identified flaws is below –
- CVE-2025-30023 (CVSS score: 9.0) – A flaw in the communication protocol used between client and server that could lead to an authenticated user performing a remote code execution attack (Fixed in Camera Station Pro 6.9, Camera Station 5.58, and Device Manager 5.32)
- CVE-2025-30024 (CVSS score: 6.8) – A flaw in the communication protocol used between client and server that could be leveraged to execute an adversary-in-the-middle (AitM) attack (Fixed in Device Manager 5.32)
- CVE-2025-30025 (CVSS score: 4.8) – A flaw in the communication protocol used between the server process and the service control that could lead to a local privilege escalation (Fixed in Camera Station Pro 6.8 and Device Manager 5.32)
- CVE-2025-30026 (CVSS score: 5.3) – A flaw in the Axis Camera Station Server that could lead to an authentication bypass (Fixed in Camera Station Pro 6.9 and Camera Station 5.58)

Successful exploitation of the aforementioned vulnerabilities could allow an attacker to assume an AitM position between the Camera Station and its clients, effectively making it possible to alter requests/responses and execute arbitrary actions on either the server or client systems. There is no evidence that the issues have been exploited in the wild.

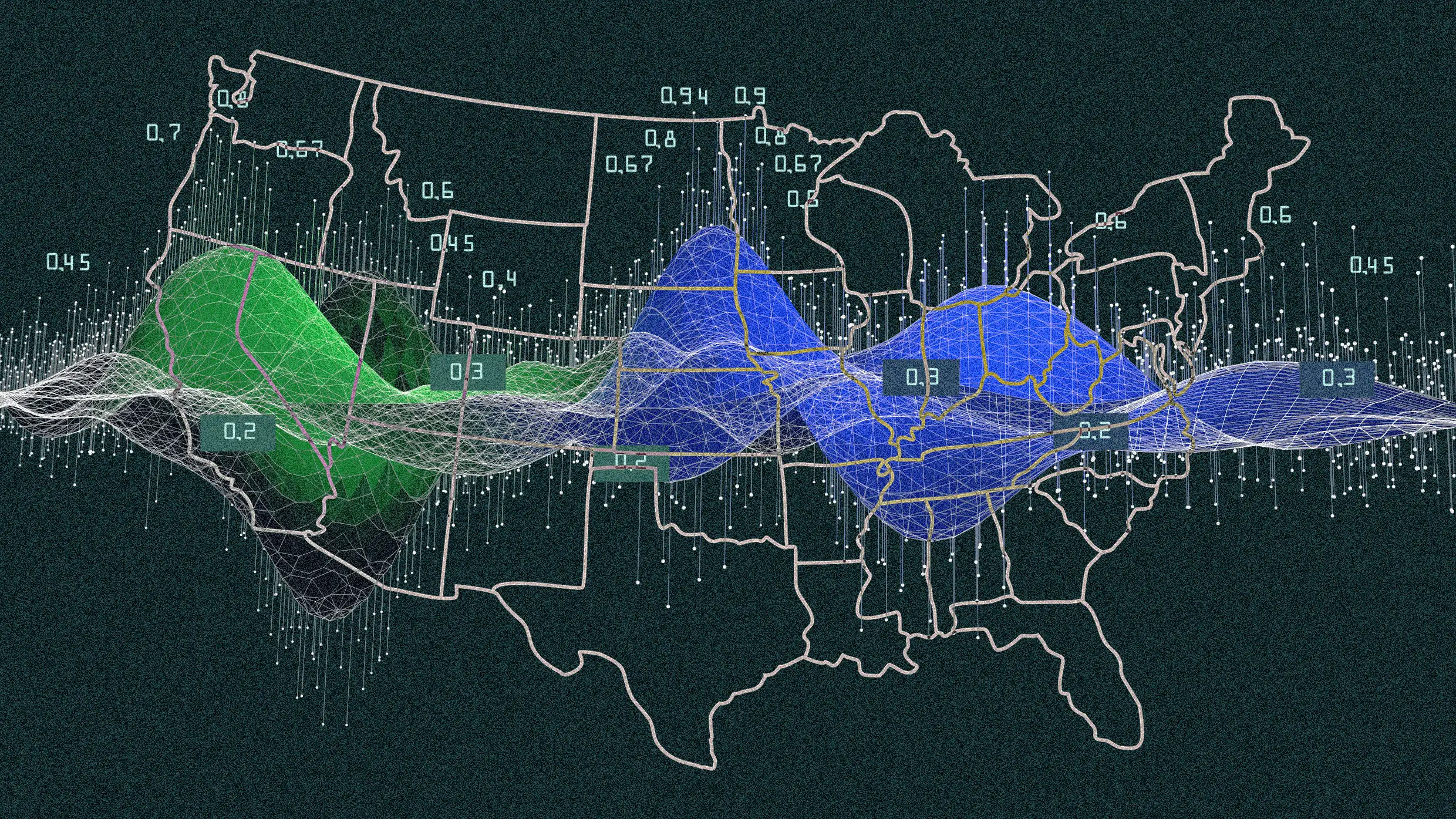
Claroty said it found more than 6,500 servers that expose the proprietary Axis.Remoting protocol and its services over the internet, out of which nearly 4,000 of them are located in the U.S.
“Successful exploits give attackers system-level access on the internal network and the ability to control each of the cameras within a specific deployment,” Moshe noted. “Feeds can be hijacked, watched, and/or shut down. Attackers can exploit these security issues to bypass authentication to the cameras and gain pre-authentication remote code execution on the devices.”