Why Pure Data Mesh Breaks at Enterprise Scale (And What Works Instead) | HackerNoon
Data Mesh claims to address data bottlenecks via decentralization, but most enterprises get bogged down in execution. Pure Data Mesh…
Kenya’s Pesalink plugs into Africa’s cross-border payments network
Kenya’s instant payments network has plugged into a continent-wide settlement system that now links more than 240 financial institutions across…
The Man Who Wrote the Rules of Freedom for Software | HackerNoon
You might have heard Linux Torvalds’ name a dozen times, but you might not have heard of Richard Stallman. And…
NXP Posts New Linux Accelerator Driver For Their Neutron NPU
The Linux kernel continues seeing more open-source kernel drivers emerge for supporting different AI accelerators / NPUs. The newest open-source…
Busha co-founder Moyo Sodipo on the making of a crypto business
The Tulia Lounge at Pan Pacific Nairobi in GTC Tower is designed for conversations that require patience. Behind the dark…
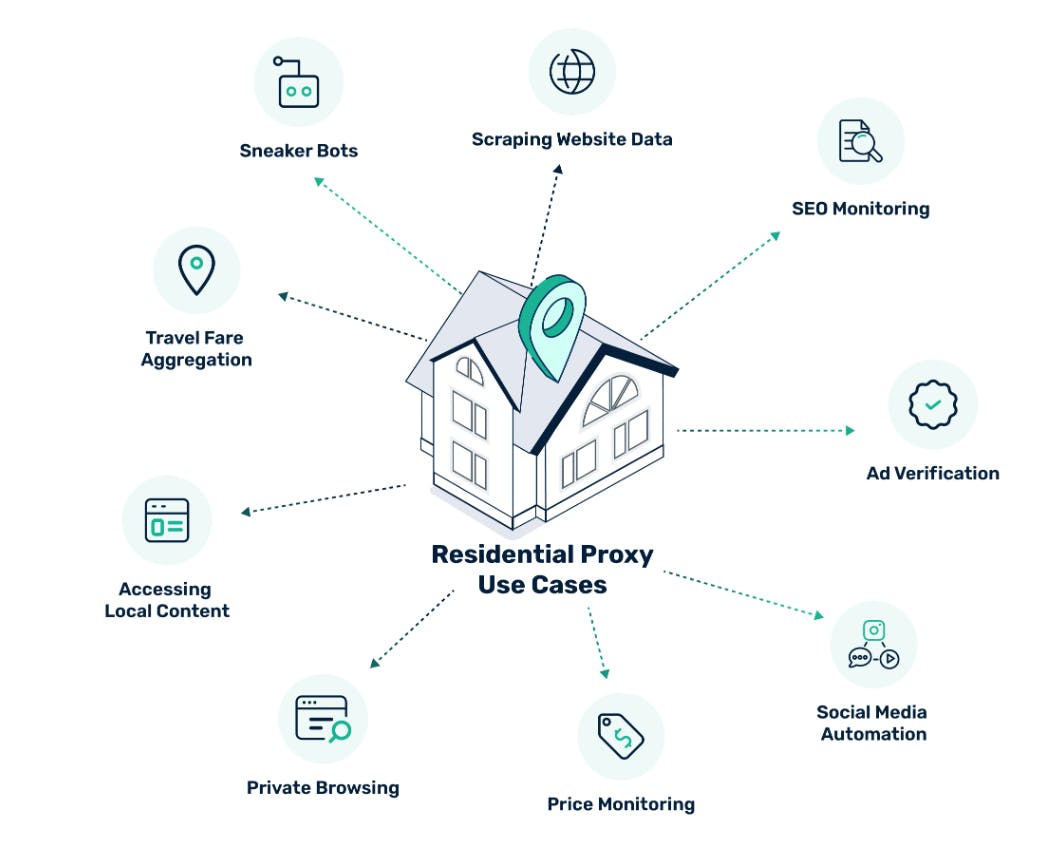
A Developer’s Guide to Residential Proxies | HackerNoon
Residential proxies are one of the most misunderstood tools in modern web development. Some developers associate them only with scraping,…
Expert Recommends: Prepare for PQC Right Now
Introduction: Steal It Today, Break It in a Decade Digital evolution is unstoppable, and though the pace may vary, things…
Linux 7.1 Looks To Support Extended Attributes On Sockets For New GNOME & systemd Functionality
While the Linux 7.0 feature merge window ended this past weekend and that next kernel release won't debut as stable…
Complete Social Media Reporting Guide + Free Template
What is a social media report?A social media report is where you gather data and make sense of it. It…
When AI DDoS’d the Real World: The Bubble Tea Incident That Exposed the Agentic Economy | HackerNoon
In February 2026, something extraordinary happened in China. An AI chatbot launched a Lunar New Year promotion offering free bubble…