How Anonymous Instagram Stories Viewing Changed My Social Media Strategy | HackerNoon
Anonymous Instagram Story viewing isn’t about stalking—it’s about strategy. This article explores how viewing public Stories without leaving a digital…
AMD RDNA3/RDNA4 Go Down Hard On Linux 6.19, But Here’s How The Older AMD GPUs End Out 2025
As part of the various end-of-year benchmarking comparisons on Phoronix and with Linux 6.19 switching older AMD GCN 1.0/1.1 graphics…
A Quiet Conversation About Our Year in Code | HackerNoon
Hey friends, As the final days of 2025 blink out on our monitors, there’s a natural pull to reflect. For…
Microsoft CTO to AI startups: Stop waiting for better models and ‘do the damned experiments’
Microsoft CTO Kevin Scott has some advice for AI startups waiting for the next breakthrough model: the technology can already…
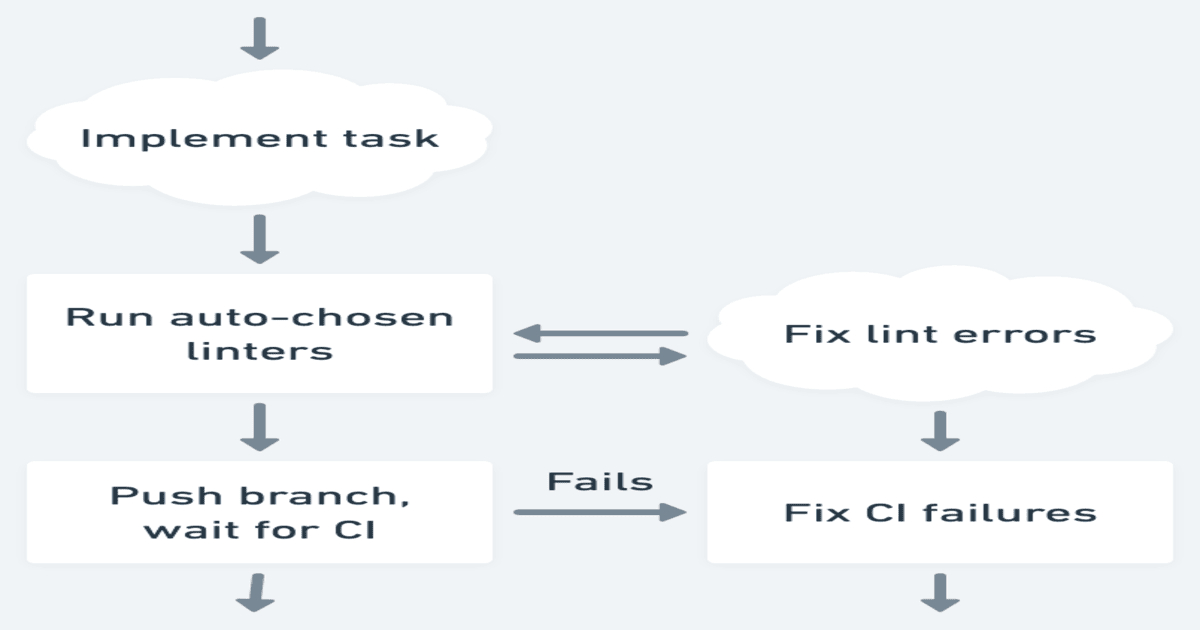
The Infinite Loop of “Fixing the Build”: How to Escape CI/CD Purgatory | HackerNoon
There is no silence quite as loud as the Slack notification channel after a failed deployment on a Friday afternoon.…
Trust Wallet Chrome Extension Breach Caused $7 Million Crypto Loss via Malicious Code
Dec 26, 2025Ravie LakshmananCryptocurrency / Incident Response Trust Wallet is urging users to update its Google Chrome extension to the…
Coreboot 25.12 Released With Qualcomm X1 Plus Platform Support, AMD Turin PoC
Coreboot 25.12 is out today as the latest quarterly feature update to this open-source BIOS/firmware solution. Coreboot 25.12 rolls out…
The Most Dangerous Person on Your Team is “Dave” (And He Just Quit) | HackerNoon
It wasn't a hacker that took down our payment gateway last year. It wasn't a DDoS attack or a memory…
Groq’s Deterministic Architecture is Rewriting the Physics of AI Inference | HackerNoon
How Nvidia Learned to Stop Worrying and Acquired Groq 0. Preface On Christmas Eve 2025, the AI world was rocked.…
China-Linked Evasive Panda Ran DNS Poisoning Campaign to Deliver MgBot Malware
A China-linked advanced persistent threat (APT) group has been attributed to a highly-targeted cyber espionage campaign in which the adversary…