hifox: Deterministic Firefox Hardening as an Enforcement Workflow | HackerNoon
You can spend an afternoon hardening Firefox and still lose confidence in the result a week later. n n The…
Tech Moves: Syndio names 7 execs; avante and Tanium add to C-suite; Amazon leaders depart
Syndio’s new leadership, top row from left: Erik Darby, Shonna Waters, Devin Luquist. Bottom row: Erin McClintock, Elizabeth Temples, Manuj…
VMUFAT File-System Driver Proposed For The Linux Kernel
The newest Linux file-system driver proposed for the kernel is... VMUFAT. Before getting too worked up about yet-another-Linux-filesystem, VMUFAT is…
China’s SAMR Opens Case to Investigate Qualcomm’s Autotalks Acquisition · TechNode
China’s State Administration for Market Regulation (SAMR) announced today that it has opened a case and launched an investigation into…
Five food and beverage influencer campaigns that delivered real ROI
How Chobani used Twitch streamers to drive 80K views Chobani built a Roblox game. That sentence alone tells you a lot…
AI Subagents: What Works and What Doesn’t | HackerNoon
I like to analyze codebases I start working on, or that I left for months. I ask my coding assistant,…
Linux 7.0 Ready For Release With Many Exciting Changes
The Linux 7.0 kernel is gearing up for its stable release and should be out this coming Sunday, 12 April,…
CES 2026: world’s first wheel-legged robot vacuum designed to tackle stairs and multi-level homes · TechNode
Roborock unveiled a concept device dubbed G-Rover at CES 2026, pitching it as the world’s first wheel-legged robot vacuum designed…
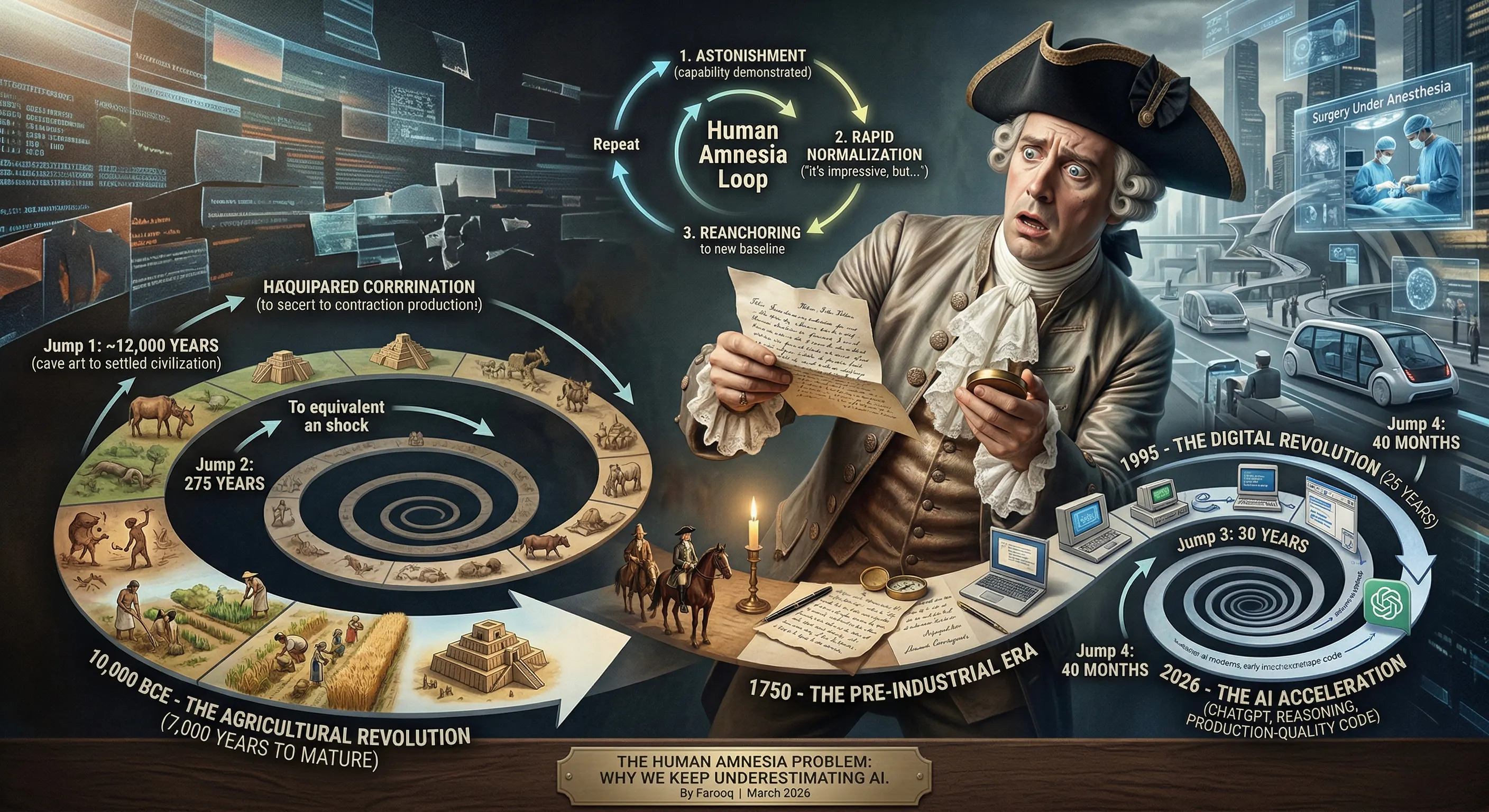
Human Amnesia Is Blinding Us to AI’s Speed | HackerNoon
There is a particular failure mode that afflicts intelligent, well-informed people more than anyone else. It is not ignorance; they…
More SpacemiT K3 RVA23 SoC Functionality Expected For Linux 7.1
The SpacemiT K3 is exciting as one of the first RISC-V RVA23 designs coming to market. For the Linux 7.0…