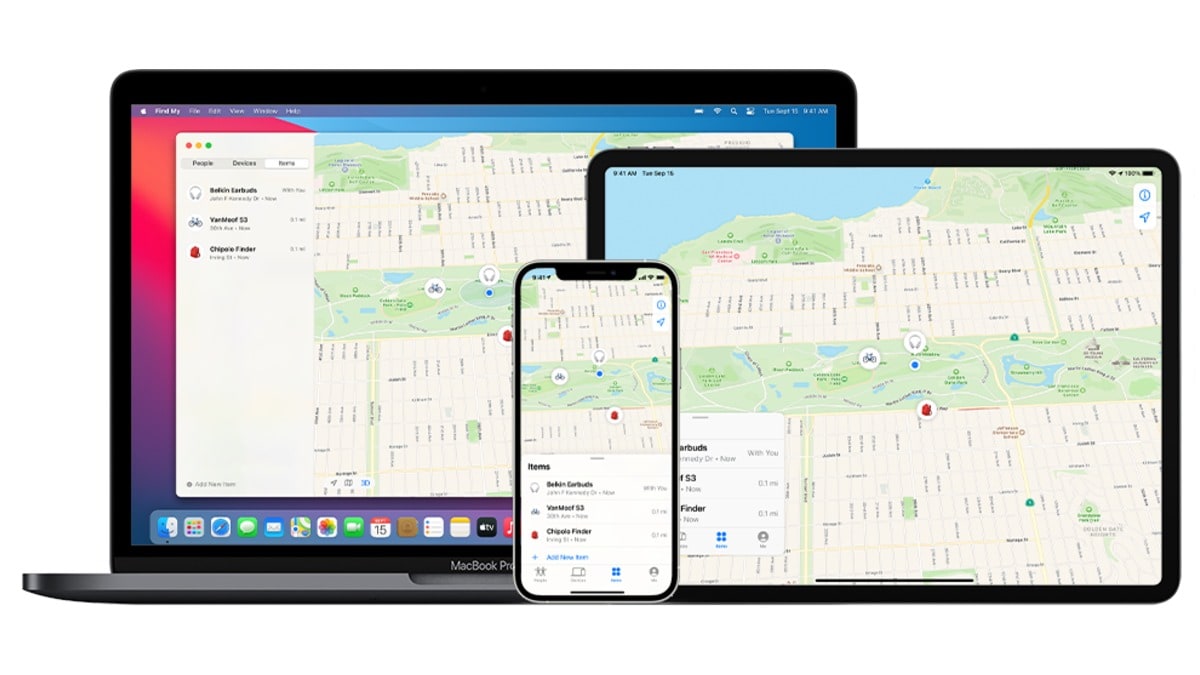
Apple’s Find My Network Can Be Used By Hackers to Track Any Device With Bluetooth Connectivity by Turning it Homing Beacons like the company’s airtag, according to resurgent. A MALICUS User Cold Trick Apple’s Find My Network INTO TRACKING A Smartphone, Laptop, or Any Internet of Things (IOT) Device Using Its Bluetooth Address, by TRICKING The Network Into Thinking An airtag. The exploit can be used to pinpoint the location of a device, or track it as it moves access a specific area.
Tricking the find my network into tracking order Ordinary Bluetooth devices
According to George Mason University Researcher Junming Chen, The Apple’s Find My Network Contains A Bluetooth Vulnerability that would allow a hacker to sill Address. Dubbed ‘Nroottag’, this Attack Tricks The Find My Network Into Thinking that a device is a loss airtag.
A team of Four Researchers LED by Chen Discovered that Nroottag Attack BE Used to identify the location of a Bluetooth Connected Device With An Accuracy of 10 Feet (3.05 metres). It could also be used to locate a larger object, such as an e-bike, and track it as it moved Around a City. The team also highlighted that the flaw could also be misused to identify the location of smart locks that have been checked, enableing attackers to Easily Find them.
While Apple Protects User Privacy on An Airtag by changing its Bluetooth address using a cryptographic key, this process required privateages. In order to circumvent this, the researchrs used Hindreds of GPUS to Identify a Key that is Compatible With the Bluetooth address of a device, and Making it adapt to the address.
The use of Several Rented GPUS offers an affordable method to quickly identify the location of a device “Within minutes”. Nroottag has a 90 percent success rate, according to the results, who say that advertising companies could avoid the use of gps and track or profile users with this technique.
While Apple’s Network was designed to track the company’s own devices, the resarchers was abled to use nroottag to track mobile devices, laptops, iot devices, SMART TVS, and Eveen Virthal Reality (Vr) Headsets. They will present these findings at the usenix security symposium in August.
The Researchers Contacted Apple About The Security Flaw in July 2024, and The Company Acknowledded their Contribution in the release notes for iOS 18.2, which was released in decision Proximity Section).
However, a proper fix for the issue – whenever it is released by apple – would likely require an update to the find my network, and might be delayed by users who defer the INSTWAREDTES on their devices. The researchers state that vulnerability in the find my network could exist for years, until these outdated devices slowly “Die out”.
Users can take some precattions to keep their devices safe from tracking, such as being judicious while granting apps access to the Bluetooth Permission or Making Sure Thei Devices ARA DeviCes ARE UN DEVICES ARE U.P. The researchers also recommend the use of privacy focused operating systems that clock potentially protect user privacy.