Table of Links
Abstract and 1. Introduction
-
Background
2.1 Ethereum Primer
2.2 Whitelisted Address Verification
2.3 Taint Analysis on Smart Contracts and 2.4 Threat Model
-
Motivating Example and Challenges
3.1 Motivating Example
3.2 Challenges
3.3 Limitations of Existing Tools
-
Design of AVVERIFIER and 4.1 Overview
4.2 Notations
4.3 Component#1: Code Grapher
4.4 Component#2: EVM Simulator
4.5 Component#3: Vulnerability Detector
-
Evaluation
5.1 Experimental Setup & Research Questions
5.2 RQ1: Effectiveness & Efficiency
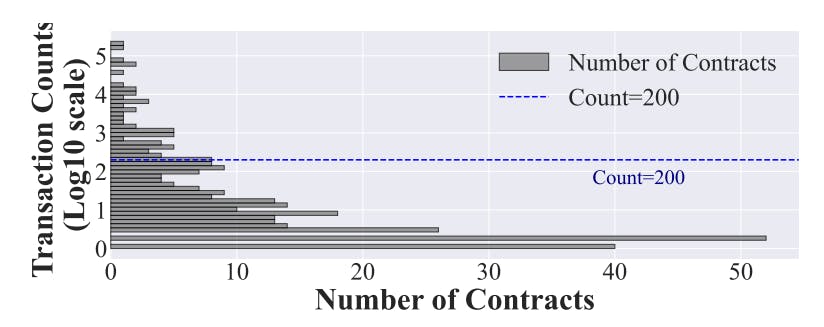
5.3 RQ2: Characteristics of Real-world Vulnerable Contracts
5.4 RQ3: Real-time Detection
-
Discussion
6.1 Threats to Validity and 6.2 Limitations
6.3 Ethical Consideration
-
Related Work
-
Conclusion, Availability, and References
4.5 Component#3: Vulnerability Detector
Based on the information collected from the Simulator, i.e., F andCT , the Detector is able to determine whether a contract is vulnerable. Specifically, as Fig. 1 illustrates, the risk detector is composed of three sequential phases, corresponding to the three principles mentioned in §3.1 (P1 to P3). We detail these three phases in the following.
4.5.1 Phase I: Whitelisted Verification Examination
Note that, the first two steps return True, indicating a whitelisted verification is inapplicable or conducted normally. In other words, only the states with the False return are kept and sent to the phase II check.
4.5.2 Phase II: External Call Check
Similarly, to avoid meaningless resource consumption, only the states that correspond to the True return value are passed to the third phase check. We regard the ones with False return value as worthless vulnerable contracts.
4.5.3 Phase III: Post-call State Modifications
4.5.4 Address Verification Vulnerable Contracts
In a nutshell, through such a three-phase detection, the Detector can effectively identify a state that can be exploited due to the existence of address verification vulnerability. We can formally summarize our detection strategy as follows.
By parsing states passed from Simulator, Detector can obtain a set of tuples, consisting of potential victims:
Through a three-phase detection, only the valuable and vulnerable states are remained:
If a contract has a state that is corresponded to a tuple in Remained, the contract is vulnerable to the address verification vulnerability.
Authors:
(1) Tianle Sun, Huazhong University of Science and Technology;
(2) Ningyu He, Peking University;
(3) Jiang Xiao, Huazhong University of Science and Technology;
(4) Yinliang Yue, Zhongguancun Laboratory;
(5) Xiapu Luo, The Hong Kong Polytechnic University;
(6) Haoyu Wang, Huazhong University of Science and Technology.