Crypto hit a strange paradox in 2025. On one hand, institutional roots deepened and user bases hit historic highs, with Binance crossing the 300 million registered users mark. On the other hand, the industry faced the industrialization of cybercrime. Web3 suffered roughly $4 billion in total losses last year, and more than half, over $2 billion, went directly to actors linked to North Korea.
We are seeing a move away from simple code exploits toward something far more dangerous. State-sponsored groups are now hitting centralized infrastructure with a level of precision that mirrors military operations. This is a distinct turning point. We have moved past the era of random, opportunistic smash-and-grabs. Instead, we are now witnessing organized financial extraction operating at a global industrial level.
North Korean Hackers Account for Most of 2025’s Web3 Losses
The numbers from 2025 reveal a disturbing efficiency in state-backed cybercrime. North Korea-linked groups stole a minimum of $2.02 billion, according to findings from Hacken’s 2025 Security Report and the Chainalysis 2026 Crypto Crime Report. Despite executing fewer individual attacks, the value of funds stolen by these actors rose 51% year-over-year. With one nation-state driving 52% of global Web3 losses, cyber theft has evolved into a critical revenue engine for the regime.
The tactics employed by groups like Lazarus have shifted away from the scattershot approach of previous years. In 2025, these actors engaged in “Big Game Hunting,” moving their focus from decentralized finance bridges to centralized infrastructure where larger pools of liquidity reside.
The compromise of Bybit stands as the year’s defining outlier event, accounting for nearly $1.5 billion of the total losses. This single breach skewed the year’s security data significantly, pushing the ratio between the largest hack and the median hack to over 1,000 times, according to Chainalysis.
These breaches rarely start with code exploits; they start with people. Brute-force hacking is out and social engineering is in. North Korean operatives have pivoted to using fake recruiter profiles and IT worker scams to physically or digitally embed themselves within crypto firms. Sometimes they get hired; other times, they trick executives into downloading malware.
By compromising the people who hold the keys to internal infrastructure, they render traditional firewalls useless. Human manipulation has become their most lethal tool.
The ‘Chinese Laundromat’
Stealing billions in digital assets is only the first phase of the operation; converting those assets into usable fiat currency without detection is the second. North Korean actors have developed a highly complex laundering pipeline to address this challenge. TRM Labs identifies this network as the Chinese laundromat, a system where DPRK actors outsource the liquidation process to a web of over-the-counter (OTC) brokers and underground banking channels.
These brokers often settle transactions in CNY or physical goods, effectively bypassing blockchain tracing mechanisms that track on-chain movement. The laundering process is methodical and patient.
Once funds are taken, they enter a complex 45-day laundering cycle. Chainalysis data maps the route these assets take, a complex journey through mixers, cross-chain bridges, and swap protocols, before they eventually exit the crypto ecosystem. It functions less like a getaway car and more like a sophisticated and transnational pipeline. The goal is to wash illicit funds so thoroughly through the global economy that tracing them back to the source becomes nearly impossible.
Stepping up Crypto Security
Combating this level of threat requires a fundamental pivot in how the industry approaches security. The focus must shift from solely auditing smart contract code to auditing operational security and human processes. As attacks target personnel and internal infrastructure, defense mechanisms must evolve to protect the human layer.
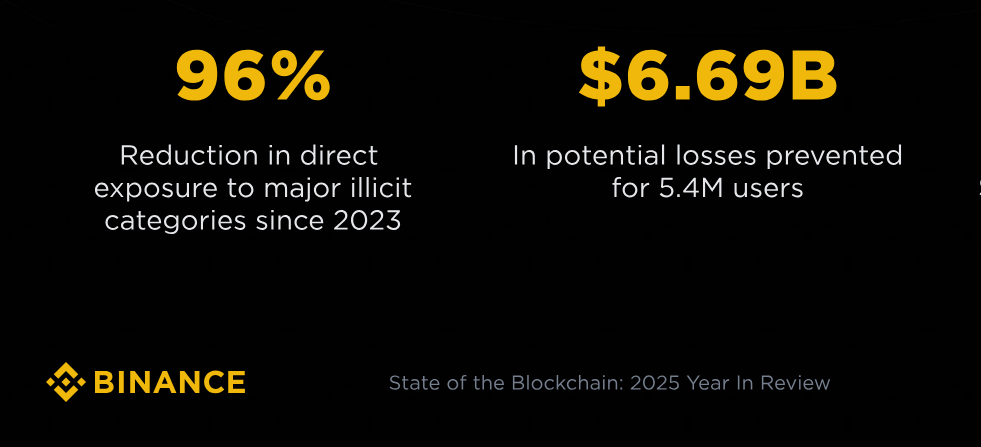
Major players are responding to these threats at scale. With over 300 million users, Binance provides a clear example of how to harden defenses against state actors. According to its 2025 Year in Review, the exchange stopped $6.69 billion in potential fraud, shielding more than 5 million users. Much of this success came from internal Red Team simulations that trained staff to spot social engineering attempts. The impact was immediate as employee phishing failure rates fell from 3.2% in 2024 to only 0.4% in 2025.
Noah Perlman, Chief Compliance Officer at Binance, emphasizes that security improvements are quantifiable even amidst massive growth.
“Analysis of independent industry data shows a steep reduction in our direct illicit exposure between early 2023 and mid-2025,” Perlman states, noting that this decline occurred despite the platform remaining the primary venue for global liquidity. He adds that this reduction was sustained “even as Binance handled volumes comparable to the next six largest exchanges combined.”
The data confirms that trust by design goes beyond a simple marketing buzzword—it’s an operational necessity. Platforms can only effectively narrow the state-sponsored attack surface by running real-time threat detection in tandem with strict compliance protocols.
Industry Safeguards Against Sophisticated Attacks
A review of the 2025 figures shows a diverging pattern. While state-sponsored actors are stealing larger sums, the industry is simultaneously closing the gap in detection and prevention. With North Korean actors driving such massive losses, the market has learned that operational resilience requires more than just auditing code.
As cryptocurrency continues its integration into the global financial system—evidenced by the surge in institutional adoption—security ceases to be merely a technical feature. It becomes the foundational requirement for the future of finance.
:::tip
This story was distributed as a release by Jon Stojan under HackerNoon’s Business Blogging Program.
:::