How are you, hacker?
🪐Want to know what’s trending right now?:
The Techbeat by HackerNoon has got you covered with fresh content from our trending stories of the day! Set email preference here.
By @n2w [ 6 Min read ]
Learn how immutable backups prevent ransomware, ensure data integrity, and meet compliance needs with secure, tamper-proof cloud data protection. Read More.
By @beldexcoin [ 4 Min read ]
BelNet introduces split tunneling for faster, more private browsing—select which data is encrypted, and enjoy speed without compromising confidentiality. Read More.
By @scylladb [ 2 Min read ]
Tripadvisor uses ML and ScyllaDB on AWS to deliver real-time personalization at massive scale with millisecond latency and advanced data architecture. Read More.
By @ozhansisic [ 11 Min read ]
Ozhan Sisic explains how to close cybersecurity governance and risk gaps by embedding security into business strategy, not just ticking compliance boxes. Read More.
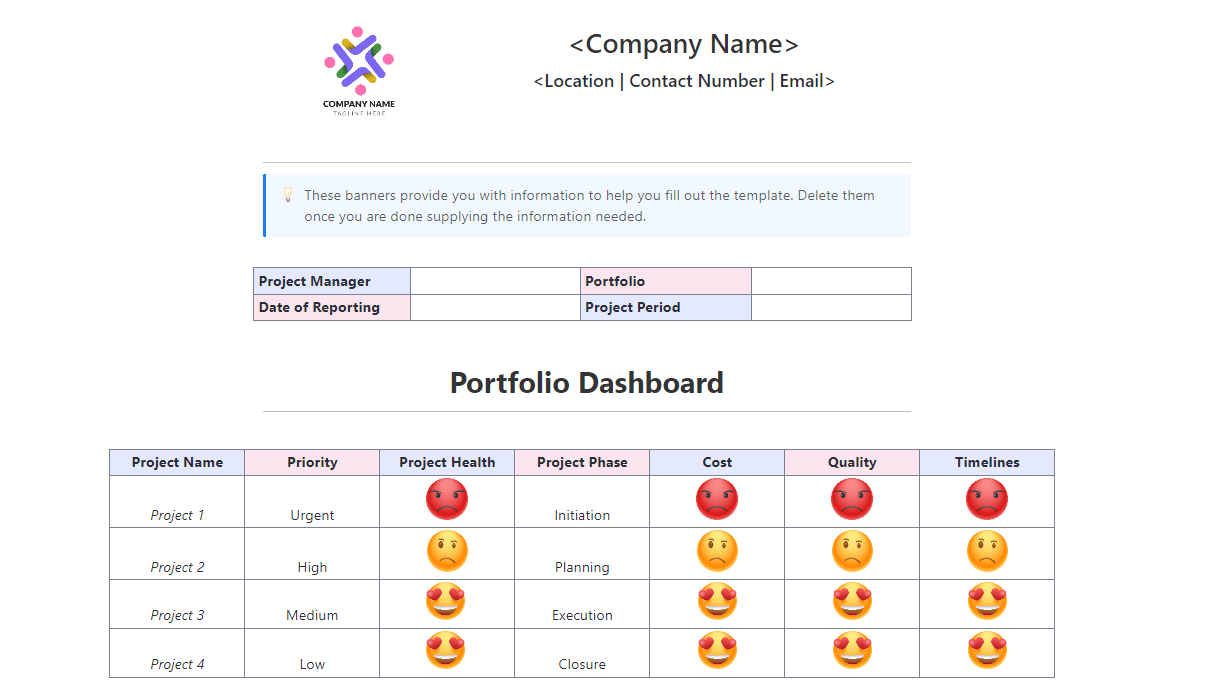
By @ivankuznetsov [ 7 Min read ]
Middle-aged PM shares his AI-powered vibe-coding setup after restarting dev journey to beat burnout. Read More.
By @mayankc [ 29 Min read ]
MCP lets AI access tools in real time—but also expands risks. This guide explores its security pitfalls and best practices for safe deployment. Read More.
By @hacker39947670 [ 13 Min read ]
Learn how EIP-7702 enables smart wallet features for existing Ethereum accounts. Complete developer guide with code examples. Read More.
By @hacker54743034 [ 8 Min read ]
AI is evolving fast, but security isn’t keeping up. Discover why zero-trust architecture is critical for safe, scalable AI agent deployment. Read More.
By @moonlock [ 11 Min read ]
Movie hacking ≠ reality: Real cyberattacks rely on phishing, not fast code. Moonlock, MacPaw’s cybersecurity division, reveals how films get it wrong. Read More.
By @ukanwat [ 7 Min read ]
Here’s why the current hype around autonomous agents is mathematically impossible and what actually works in production. Read More.
By @hacker42316417 [ 8 Min read ]
Learn how to automate KYC with Google Cloud’s Document AI and Vertex AI—extract data, verify identities, and score risks in seconds. Read More.
By @maxnechaev [ 10 Min read ]
Fragile, chaotic AI agents are everywhere. AAC is a simple yet powerful architecture that brings structure, scalability, and reliability to your agent systems. Read More.
By @penworth [ 4 Min read ]
Zak Taher has spent over 2 decades in the industry guiding teams and businesses through transformation, volatility, and innovation. Read More.
By @bolshiyanov [ 52 Min read ]
Your collaborative AI assistant to design, iterate, and scale full-stack applications for the web. Read More.
By @badmonster0 [ 5 Min read ]
Learn how to build a scalable face recognition pipeline with CocoIndex—from detecting faces to running real-time similarity searches in a vector database. Read More.
By @iamshvetsov [ 5 Min read ]
In this article, I’ve shared a hypothesis about a short liquidity pool and proposed a basic implementation in Solidity for the Ethereum blockchain. Read More.
By @kashvipandey [ 4 Min read ]
Dogecoin eyes $0.50, but Little Pepe (LILPEPE) is surging with a $8.5M presale and its own Pepe Chain, positioning as the next big meme coin ecosystem. Read More.
By @birdsandbricks [ 35 Min read ]
This piece draws powerful connections between artificial intelligence and The Matrix, examining how data exploitation, simulated realities, and algorithmic cont Read More.
By @maken8 [ 6 Min read ]
In this article, my co-author and I explore how Bitcoin would revolutionize the same electricity network it is backed by. Read More.
By @flashpr [ 3 Min read ]
Nexchain isn’t just another Layer 1 pitch. It’s designed from the ground up to address key bottlenecks in blockchain performance Read More.
🧑💻 What happened in your world this week? It’s been said that writing can help consolidate technical knowledge, establish credibility, and contribute to emerging community standards. Feeling stuck? We got you covered ⬇️⬇️⬇️
ANSWER THESE GREATEST INTERVIEW QUESTIONS OF ALL TIME
We hope you enjoy this worth of free reading material. Feel free to forward this email to a nerdy friend who’ll love you for it.
See you on Planet Internet! With love,
The HackerNoon Team ✌️

.gif?auto=format&fit=max&w=3840)