For a long time, developing advanced malware seemed reserved for actors with experience, time and considerable technical capacity, especially in an environment in which operating systems and many platforms have been tightening their defenses. But the table is changing. What we have seen in recent years is that artificial intelligence not only serves to summarize texts or answer questions, it can also very visibly accelerate the software creation when given precise instructions. And that leaves us facing a reality that is difficult to ignore: the same tool that simplifies legitimate tasks can also reduce part of the effort necessary to create malicious code.
That change begins to take concrete form with VoidLink. In its analysis, Check Point presents it as one of the strongest evidence so far of advanced malware developed largely with the help of AI. There is, however, an important nuance in the investigation itself: the company assures that it detected it at an early stage, that it was not deployed against victims and that it was not used in active attacks. But that is precisely why the discovery is so revealing, because it allowed access to development materials that rarely come to light.
How VoidLink was built and why it changes the dashboard
VoidLink was not, at least on paper, a minor piece or a rudimentary experiment. The cybersecurity firm describes it as a malware framework for Linux with a modular architecture, designed to maintain stealthy and prolonged access in cloud environments. In his analysis he mentions components such as eBPF and LKM rootkits, as well as specific modules for cloud enumeration and subsequent activities in container environments. That level of maturity is just what separates it from other previous cases associated with simpler code.
One of the most striking twists in the case is who seems to have been behind it. Check Point explains that, due to its internal structure and the pace of evolution observed, VoidLink gave the impression of having come from a large team, with different profiles and a fairly defined work plan. But the evidence collected by the firm points to something very different: a single actor who, according to the investigation, would have had AI support during different phases of development. There is also another relevant element: that actor would not be a rookie, but rather someone with a solid technical base and previous experience in cybersecurity.
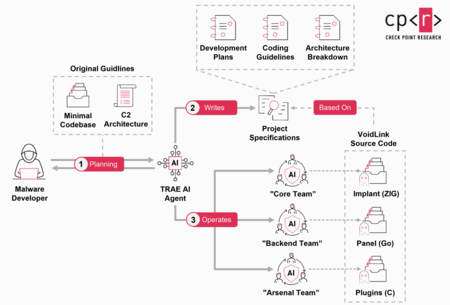
Rebuilding Workflow Attributed to VoidLink | Image: Check Point
The most revealing part of the case is how the project would have been built. The firm describes a working method based on what it calls Spec Driven Development that works as follows:
- You define what you want to build.
- That idea is translated into architecture, tasks, sprints and delivery criteria.
- The implementation is delegated to the model.
In the exposed materials, development plans, technical documentation, coding standards, deployment and testing guides appeared, as well as an organization by teams and phases that supports this model. One of the recovered artifacts, dated December 4, 2025, further suggests that VoidLink had already reached a functional phase in less than a week and exceeded the 88,000 lines of code.

That is precisely what separates VoidLink from other precedents. Check Point maintains that this is the strongest evidence of malware created almost entirely with the help of AI. “This is the first confirmed case of advanced AI-generated malware, created with the speed, structure and sophistication of an entire engineering organization,” the company says. The question now is how far malicious actors can go with these types of techniques.
Images | WorldOfSoftware with Nano Banana | Check Point
In WorldOfSoftware | The Booking hack is a little more disturbing: “Tracking phishing” attacks are here to stay