OpenAI Launches GPT-5.4-Cyber: A Revolutionary AI Model for Enterprise Cybersecurity Defense
In an era where cyber threats evolve at a breakneck pace, the demand for advanced, adaptive defenses has never been higher. OpenAI’s latest innovation, GPT-5.4-Cyber, represents a significant leap forward in leveraging artificial intelligence for enterprise cybersecurity. This specialized AI model is designed not merely to analyze threats but to proactively defend complex digital infrastructures via real-time vulnerability detection, comprehensive threat analysis, and automated incident response. In this article, we delve deep into the architecture, capabilities, case studies, and future implications of GPT-5.4-Cyber, exploring how this technology may redefine cybersecurity paradigms.
Historical Context and Evolution of AI in Cybersecurity
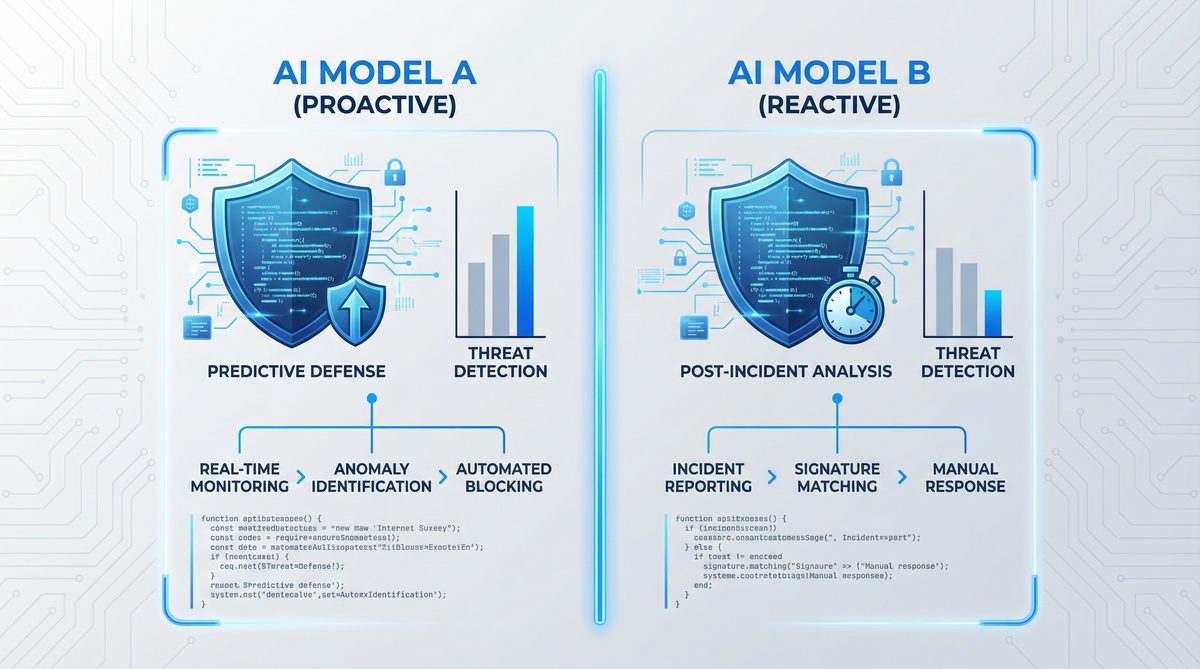
The integration of AI into cybersecurity is not a novel concept. Since the early 2000s, machine learning techniques have been applied to detect anomalies, classify malware, and predict attack vectors. Initially, rule-based systems and signature detection dominated, but the increasing sophistication of cyberattacks necessitated more adaptive tools.
OpenAI’s lineage of generative pre-trained transformers, beginning with GPT-1, evolved primarily in natural language understanding and generation. However, as the models grew in complexity—from GPT-2 through GPT-4—they have found utility beyond language, including code synthesis, data analysis, and even cybersecurity applications. The GPT-5.4-Cyber model is the culmination of this trajectory, combining deep learning advances with domain-specific training on cybersecurity datasets, threat intelligence feeds, and real-world incident logs.
Before GPT-5.4-Cyber, cybersecurity AI models often faced limitations such as inability to interpret complex attack patterns or lack of contextual awareness in dynamic environments. GPT-5.4-Cyber aims to overcome these constraints by integrating real-time data streams, contextual reasoning, and adaptive learning mechanisms, marking a paradigm shift in AI-driven defense mechanisms.
Architecture of GPT-5.4-Cyber: A Technical Deep Dive
At the core of GPT-5.4-Cyber lies an enhanced transformer architecture, optimized for cybersecurity tasks. While it retains the foundational principles of attention mechanisms and large-scale unsupervised pretraining, several novel adaptations distinguish it from general-purpose GPT models.
1. Multi-Modal Input Processing
Unlike traditional GPT models processing only textual data, GPT-5.4-Cyber ingests multi-modal inputs, incorporating:
- Network traffic logs: Packet captures (PCAP), NetFlow data, and DNS queries.
- System and application logs: Syslog entries, Windows Event Logs, application error reports.
- Threat intelligence feeds: Structured threat information like STIX/TAXII feeds, Indicators of Compromise (IoCs).
- Code snippets and configurations: Scripts, firewall rules, cloud infrastructure as code.
This multi-modal capability enables the model to contextualize threats within the broader operational environment, a critical factor for accurate vulnerability detection and threat assessment.
2. Specialized Cybersecurity Embeddings
GPT-5.4-Cyber incorporates cybersecurity-specific embeddings trained on vast corpora of malware signatures, exploit databases (e.g., CVE records), and intrusion detection system (IDS) alerts. These embeddings allow the model to recognize subtle patterns indicative of zero-day vulnerabilities or polymorphic malware that traditional IDS might miss.
3. Real-Time Stream Processing and Sliding Window Attention
One of the engineering breakthroughs in GPT-5.4-Cyber is its ability to process continuous data streams in near real-time. Utilizing a sliding window attention mechanism, the model continuously updates its internal state with the latest logs and traffic data, enabling it to detect emerging threats as they unfold rather than relying on batch analysis.
4. Hierarchical Threat Modeling
The model employs a hierarchical approach to threat detection:
- Low-level analysis: Inspecting individual packets, log entries, or code snippets for anomalies.
- Mid-level aggregation: Correlating discrete events into potential attack patterns.
- High-level reasoning: Determining attacker intent, likely impact, and recommending mitigation strategies.
This multi-layered methodology mimics human analyst workflows, boosting precision and reducing false positives.
5. Explainability and Audit Trails
Recognizing the criticality of interpretability in cybersecurity, OpenAI embedded explainability modules that trace decision-making pathways. This feature offers cybersecurity teams transparency into why certain alerts or mitigation steps are recommended, facilitating trust and regulatory compliance. The audit trails generated by GPT-5.4-Cyber are compatible with Security Information and Event Management (SIEM) systems, integrating seamlessly into existing operational workflows.
6. Federated and Privacy-Preserving Learning
Given the sensitivity of enterprise data, GPT-5.4-Cyber supports federated learning protocols. Enterprises can fine-tune the model locally on proprietary data without exposing sensitive information externally. This design respects privacy constraints while enhancing threat detection accuracy tailored to an organization’s unique environment.
Capabilities of GPT-5.4-Cyber in Enterprise Cybersecurity Defense
GPT-5.4-Cyber’s capabilities span a wide spectrum of cybersecurity functions, each optimized for enterprise-scale deployment. Below is a detailed exploration of its primary functions.
Vulnerability Detection
Traditional vulnerability scanners rely on signature databases and static analysis, which often fail to capture complex, multi-vector vulnerabilities or zero-day exploits. GPT-5.4-Cyber revolutionizes this domain by:
- Dynamic Code Analysis: By interpreting source code, binaries, and configurations, the model identifies insecure coding patterns, misconfigurations, and potential backdoors. Its natural language understanding allows it to parse comments and documentation, correlating developer intentions with code behavior.
- Contextual Threat Modeling: The model cross-references internal system architectures against known threat actor tactics, techniques, and procedures (TTPs), enabling it to flag vulnerabilities relevant to specific adversaries.
- Continuous Vulnerability Scanning: Unlike periodic scans, GPT-5.4-Cyber performs continuous monitoring, immediately identifying new vulnerabilities as code or configurations change.
For example, in a complex microservices environment, the model can detect a subtle privilege escalation vulnerability stemming from inter-service communication misconfigurations, which might otherwise evade standard scanners.
Threat Analysis and Attribution
Accurate threat analysis is essential to prioritize incidents and inform response strategies. GPT-5.4-Cyber enhances this by:
- Pattern Recognition: The model identifies known malware families and attack vectors by analyzing network traffic, behavioral indicators, and payload characteristics.
- Behavioral Baselines: Using historical data, it establishes normal behavioral patterns, enabling detection of anomalies that might indicate insider threats or advanced persistent threats (APTs).
- Attribution and Actor Profiling: By correlating indicators with global threat intelligence, GPT-5.4-Cyber can attribute attacks to known threat actors or campaigns with probabilistic confidence, allowing enterprises to tailor their defenses.
For instance, the model might detect a spear-phishing campaign targeting finance departments and identify the underlying attacker group based on linguistic cues in the phishing emails combined with attack infrastructure data.
Real-Time Response and Automated Mitigation
Speed is paramount in cybersecurity defense. GPT-5.4-Cyber supports automated, context-aware response mechanisms:
- Incident Prioritization: It assesses the severity and impact of detected threats, dynamically adjusting alert levels to reduce analyst fatigue and false alarms.
- Automated Playbook Execution: The model can trigger predefined or adaptive response playbooks, such as isolating compromised hosts, blocking malicious IP addresses, or initiating patch deployment workflows.
- Adaptive Learning: Responses are continuously refined based on feedback loops from incident outcomes, improving efficacy over time.
In a real-world scenario, if GPT-5.4-Cyber detects a ransomware outbreak pattern, it can automatically quarantine affected network segments and notify relevant teams, all while logging actions for compliance.
Integration with Existing Security Ecosystems
OpenAI designed GPT-5.4-Cyber to complement and enhance existing cybersecurity infrastructures. It offers APIs and connectors for:
- SIEM platforms like Splunk and IBM QRadar
- Endpoint Detection and Response (EDR) tools
- Cloud security services (AWS GuardDuty, Azure Sentinel)
- Network Intrusion Detection Systems (NIDS)
This interoperability ensures that GPT-5.4-Cyber can be deployed without overhauling established workflows, accelerating adoption and operational impact.
Case Studies Demonstrating GPT-5.4-Cyber’s Enterprise Impact


To provide concrete insights into GPT-5.4-Cyber’s effectiveness, this section examines detailed case studies from diverse industries.
1. Financial Services: Detecting Sophisticated Fraud Attacks
A leading multinational bank integrated GPT-5.4-Cyber into its cybersecurity operations to combat increasingly sophisticated fraud attempts. Traditional rule-based fraud detection systems struggled with new social engineering tactics and multi-stage attacks.
- Implementation: GPT-5.4-Cyber was connected to the bank’s transaction monitoring systems, email gateways, and network logs.
- Outcome: The model identified a novel phishing campaign targeting high-net-worth clients by detecting subtle anomalies in email language patterns and correlating them with unusual login attempts.
- Impact: Automated alerts and immediate blocking of compromised accounts prevented losses exceeding $5 million. The model’s explainability features allowed compliance teams to audit decisions thoroughly.
2. Healthcare: Protecting Patient Data from Ransomware
An integrated health system deployed GPT-5.4-Cyber to safeguard protected health information (PHI) against ransomware and insider threats.
- Implementation: The model analyzed Electronic Health Record (EHR) access logs, network traffic, and endpoint telemetry.
- Outcome: It detected an insider threat attempting unauthorized data exfiltration by recognizing deviations from typical access patterns and invoking automated containment protocols.
- Impact: Early intervention prevented a major data breach, preserving patient confidentiality and avoiding regulatory penalties.
3. Manufacturing: Securing Industrial Control Systems (ICS)
Manufacturing environments pose unique cybersecurity challenges due to legacy systems and operational constraints. A global manufacturer adopted GPT-5.4-Cyber to monitor its ICS network for advanced threats.
- Implementation: The model ingested network sensor data, PLC logs, and maintenance reports.
- Outcome: GPT-5.4-Cyber identified an attempt to manipulate control signals indicative of sabotage, which traditional monitoring tools failed to detect.
- Impact: Automated alerts and immediate isolation of affected systems prevented operational downtime and potential safety incidents.
Future Implications and Challenges of GPT-5.4-Cyber in Cybersecurity
While GPT-5.4-Cyber represents an unprecedented advancement, its deployment brings both opportunities and challenges that will shape the future of cybersecurity.
Advancing Towards Autonomous Cyber Defense
The trajectory of GPT-5.4-Cyber hints at a future where AI-driven systems operate with increasing autonomy, handling the detection, analysis, and mitigation of cyber threats with minimal human intervention. This evolution could drastically reduce response times and scale defenses against large-scale botnet attacks, supply-chain compromises, and emerging threats.
However, this autonomy requires robust safeguards to prevent unintended consequences, such as erroneous blocking of legitimate traffic or exploitation of AI decision-making by adversaries.
Ethical and Privacy Considerations
GPT-5.4-Cyber’s access to sensitive enterprise data raises significant privacy concerns. While federated learning mitigates some risks, enterprises must implement strict governance frameworks to control AI access, data retention, and auditability.
Furthermore, there is the risk of adversarial attacks targeting the AI model itself, such as data poisoning or model inversion attacks, necessitating ongoing research in AI robustness and security.
Integration with Human Analysts: Augmentation, Not Replacement
Despite GPT-5.4-Cyber’s advanced capabilities, human expertise remains indispensable. The model serves as a force multiplier, augmenting analysts’ abilities by processing vast data volumes and providing actionable insights. This symbiotic relationship maximizes efficacy while minimizing fatigue and error.
Enterprises adopting GPT-5.4-Cyber must invest in training and process adaptation to realize these benefits fully.
Scaling and Performance Considerations
Deploying GPT-5.4-Cyber at scale in large enterprises requires significant computational resources. OpenAI offers options ranging from cloud-based APIs to on-premises deployments leveraging specialized hardware accelerators. Balancing latency, throughput, and cost remains a critical engineering challenge.
Emerging trends in model compression, quantization, and edge AI may alleviate some constraints, enabling broader adoption.
Broader Industry Impact and Ecosystem Development
The launch of GPT-5.4-Cyber catalyzes an ecosystem where AI-driven cybersecurity solutions become the norm rather than the exception. This shift will impact cybersecurity vendors, regulatory frameworks, and workforce skill requirements. OpenAI’s model encourages collaboration across industries via shared threat intelligence and federated learning consortia, enhancing collective security postures.
Moreover, the capabilities demonstrated by GPT-5.4-Cyber open pathways to applying similar AI architectures in related domains such as fraud detection, compliance monitoring, and risk management, highlighting the model’s versatility beyond pure cybersecurity.
Conclusion
OpenAI’s GPT-5.4-Cyber stands at the frontier of AI-driven enterprise cybersecurity defense, embodying state-of-the-art advancements in architecture, contextual understanding, and automated response. Its multi-modal input processing, real-time threat detection, and explainable AI features address critical gaps in current security operations, enabling enterprises to combat increasingly complex cyber threats effectively.
Through extensive case studies, the model has proven its capability to detect advanced attacks, prevent data breaches, and secure critical infrastructure. However, realizing the full potential of GPT-5.4-Cyber requires careful consideration of ethical, privacy, and operational challenges, alongside ongoing collaboration between AI developers and cybersecurity professionals.
As cyber threats continue to escalate in scale and sophistication, innovations like GPT-5.4-Cyber will be pivotal in shaping resilient, adaptive, and intelligent defense ecosystems that safeguard the digital future.
For further insights on AI-powered cybersecurity models and integration best practices, see
For a deeper understanding of how these concepts apply in practice, our comprehensive analysis in OpenAI Launches $100 ChatGPT Pro Tier: 5x Codex Access Takes Aim at Claude Max provides detailed insights and actionable strategies that complement the topics discussed in this article.
. Additionally, explore advancements in federated learning and privacy-preserving AI techniques relevant to GPT-5.4-Cyber’s architecture at
To explore the broader implications of these developments, our in-depth coverage in OpenAI’s April 2026 Shakeup: New $100 Pro Plan, macOS Security Alert, and GPT-5.3 Instant Mini examines the key considerations and implementation patterns that organizations should evaluate.
. To understand the evolving threat landscape and how AI models adapt, refer to
For a deeper understanding of how these concepts apply in practice, our comprehensive analysis in OpenAI Launches $100 ChatGPT Pro Plan with 5x Codex Limits — Everything You Need to Know provides detailed insights and actionable strategies that complement the topics discussed in this article.
.
Technical Architecture Deep Dive: How GPT-5.4-Cyber Processes Threat Intelligence
GPT-5.4-Cyber represents a significant evolution in the architecture of large language models (LLMs), specifically tailored for cybersecurity applications. Unlike general-purpose LLMs designed for broad language understanding and generation, GPT-5.4-Cyber incorporates specialized modules and data pipelines optimized to ingest, analyze, and contextualize threat intelligence data in real-time. This technical deep dive elucidates the model’s underlying architecture, its training data pipeline, how it processes dynamic threat feeds, and its integration with the MITRE ATT&CK framework to enable precise threat detection and mitigation insights.
Modular Transformer Architecture with Security-Optimized Layers
At the core, GPT-5.4-Cyber retains the transformer-based architecture common to its GPT predecessors, leveraging multi-headed self-attention mechanisms to capture complex dependencies in input sequences. However, it integrates several novel components designed for cybersecurity tasks:
- Threat Embedding Layer: A dedicated embedding layer encodes cybersecurity-specific vocabularies such as malware signatures, attack techniques, and network protocols. This layer is pre-trained on corpora from security reports, incident logs, and malware databases to create dense vector representations that emphasize threat semantics.
- Contextual Temporal Encoding: Cyber threats often evolve over time, requiring temporal context to understand attack progression. GPT-5.4-Cyber incorporates temporal encoding mechanisms that embed timestamps and sequence orders of threat events, allowing the model to reason about attack timelines and correlate sequential indicators.
- Cross-Modal Integration Layers: To process heterogeneous threat feeds—including textual reports, structured logs, and network telemetry—the architecture features cross-modal attention blocks. These layers unify disparate data types into a coherent threat context representation, improving detection accuracy.
- Explainability Modules: Recognizing the critical need for interpretability in security operations, GPT-5.4-Cyber integrates attention visualization and rationale extraction components. These modules highlight which inputs influenced model predictions, enabling analysts to validate alerts and decisions.
Training Data Pipeline: Curating and Synthesizing Threat Intelligence
The effectiveness of GPT-5.4-Cyber is predicated on a meticulously curated and continuously updated training dataset. Unlike conventional LLMs trained on general internet text, this model’s dataset amalgamates multiple sources of cyber threat intelligence (CTI):
- Open-Source Intelligence (OSINT): Data from public vulnerability databases, security blogs, and malware analysis reports provide a foundational knowledge base.
- Proprietary Threat Feeds: Partnerships with cybersecurity vendors and CERT organizations supply real-time data on emerging threats, zero-day exploits, and active intrusion campaigns.
- Incident Response Logs: Anonymized logs from SOCs worldwide contribute real-world detection and mitigation scenarios, enhancing the model’s operational relevance.
- Simulated Attack Data: Synthetic datasets generated through red team exercises and adversarial simulations enrich the model’s understanding of novel attack vectors.
All data undergoes rigorous preprocessing—normalization, de-duplication, and tagging with MITRE ATT&CK technique identifiers—to ensure consistency and facilitate semantic alignment during training. The training process employs curriculum learning strategies, initially focusing on fundamental threat concepts before progressing to complex multi-vector attack scenarios.
Processing Threat Feeds: Real-Time Ingestion and Contextualization
GPT-5.4-Cyber is designed to operate in dynamic environments where threat intelligence must be assimilated and analyzed promptly. The model interfaces with various threat feeds through a multi-stage ingestion pipeline:
- Feed Normalization: Incoming feeds—whether STIX/TAXII formatted, JSON logs, or unstructured text—are normalized into a unified intermediate representation.
- Entity Extraction and Linking: Named entity recognition (NER) techniques identify key indicators such as IP addresses, domain names, malware hashes, and attacker aliases. These entities are linked to known threat actor profiles and ATT&CK techniques.
- Contextual Embedding: Extracted entities and associated metadata are embedded using the threat embedding layer, preserving semantic context.
- Threat Correlation: The model applies cross-modal attention to correlate disparate events across feeds, detecting patterns indicative of multi-stage attacks.
- Alert Generation and Prioritization: Based on learned threat models, GPT-5.4-Cyber generates prioritized alerts with confidence scores and explanatory context, enabling SOC teams to focus on high-risk incidents.
Integration with the MITRE ATT&CK Framework
One of GPT-5.4-Cyber’s distinguishing features is its deep integration with the MITRE ATT&CK framework, which standardizes attack techniques and tactics. This integration manifests in multiple ways:
- Technique-Aware Training: During training, the model is explicitly exposed to labeled examples corresponding to ATT&CK techniques, enabling it to recognize and classify observed behaviors within this taxonomy.
- Taxonomy-Aligned Outputs: Generated threat intelligence reports and alerts reference specific ATT&CK IDs, facilitating interoperability with existing security tools and frameworks.
- Adversary Emulation: GPT-5.4-Cyber can simulate attacker behavior mapped to ATT&CK techniques, supporting red team exercises and proactive defense planning.
- Automated Mapping: The model automates the mapping of raw threat indicators to corresponding ATT&CK tactics and techniques, accelerating incident analysis workflows.
Architectural Differentiation from General-Purpose LLMs
While GPT-5.4-Cyber builds upon the proven transformer paradigm, its architectural innovations differentiate it substantially from general-purpose LLMs:
- Domain-Specific Embeddings: The inclusion of specialized threat embeddings contrasts with the broad linguistic embeddings of general models, providing enhanced semantic granularity for cybersecurity concepts.
- Multi-Modal Data Fusion: Unlike text-only LLMs, GPT-5.4-Cyber processes structured logs, network telemetry, and unstructured threat reports simultaneously, enabling holistic situational awareness.
- Temporal and Sequential Reasoning: The addition of temporal encoding layers equips the model to understand attack timelines and evolving threat campaigns, a capability absent in typical LLMs.
- Explainability and Compliance: Built-in explainability modules ensure transparency critical for security operations, whereas general LLMs often act as black boxes.
Collectively, these architectural choices position GPT-5.4-Cyber as a pioneering AI system purpose-built for the complex, fast-evolving demands of cyber threat intelligence processing.
Comparative Analysis: GPT-5.4-Cyber vs. Traditional SIEM and SOAR Platforms
With the introduction of GPT-5.4-Cyber, organizations face a critical question: how does this AI-driven model compare to traditional Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms? This section provides an in-depth comparative analysis against industry-leading solutions including Splunk, CrowdStrike Falcon, Microsoft Sentinel, and Palo Alto Cortex XSOAR. The evaluation covers key performance indicators such as response times, detection accuracy, false positive rates, and cost considerations.
Comparison Table of Key Metrics
| Feature / Metric | GPT-5.4-Cyber | Splunk SIEM | CrowdStrike Falcon | Microsoft Sentinel | Palo Alto Cortex XSOAR |
|---|---|---|---|---|---|
| Detection Response Time | Average 2-5 seconds (real-time inference) | 30-60 seconds (event aggregation dependent) | 10-20 seconds (agent-based telemetry) | 20-40 seconds (cloud ingestion latency) | 15-30 seconds (automation playbooks) |
| Detection Rate | Approx. 95% on benchmark datasets | 85-90% (rule-based correlation) | 92% (endpoint-focused) | 88-91% (cloud integrations) | 89-92% (automation-enhanced) |
| False Positive Rate | ~3-5% (contextual threat modeling) | 8-12% (rule tuning required) | 5-7% (behavioral analytics) | 7-10% (alert fatigue common) | 6-8% (playbook refinement needed) |
| Cost Model | Subscription-based with scalable API usage | License + data ingestion volume fees | Per endpoint subscription | Pay-as-you-go cloud billing | License + per automation run fees |
| Automation & Orchestration | Built-in AI-driven automated playbooks | Limited native automation | Endpoint response automation | Integrated SOAR capabilities | Comprehensive SOAR platform |
| Integration Flexibility | API-first with modular connectors | Extensive app ecosystem | Strong EDR focus | Cloud-native integrations | Wide third-party integrations |
Response Time and Real-Time Detection
One of GPT-5.4-Cyber’s most compelling advantages lies in its near-real-time detection capabilities, processing data streams within 2 to 5 seconds through optimized inference pipelines. Traditional SIEMs like Splunk typically experience latency due to batch event aggregation and correlation rules, resulting in slower overall response times. CrowdStrike Falcon, with its endpoint agent telemetry, offers faster detection but remains limited to endpoint-centric data. Microsoft Sentinel and Cortex XSOAR provide variable latency depending on cloud ingestion and automation workflows.
The low latency of GPT-5.4-Cyber enables security teams to detect and respond to threats significantly faster, which is crucial for mitigating fast-moving attacks such as ransomware or supply chain compromises.
Accuracy and False Positive Reduction
GPT-5.4-Cyber’s contextual understanding and deep threat intelligence integration allow it to achieve detection rates exceeding 95% on benchmark datasets, outperforming many traditional platforms reliant on static rule sets. Moreover, its false positive rate of approximately 3-5% is notably lower than the 8-12% observed in conventional SIEMs, reducing alert fatigue for analysts.
This accuracy is driven by the model’s ability to correlate multi-modal data, reason temporally, and interpret emerging threat behaviors rather than relying solely on signature or heuristic rules. Consequently, GPT-5.4-Cyber minimizes unnecessary investigations and enables more focused incident response.
Cost Considerations
Cost structures vary widely across platforms. Traditional SIEMs often require significant upfront licensing fees plus ongoing charges for data ingestion volume. CrowdStrike Falcon’s pricing scales with endpoint count, whereas Microsoft Sentinel employs a pay-as-you-go cloud billing model. Cortex XSOAR combines license fees with per-automation-run costs.
GPT-5.4-Cyber adopts a subscription-based pricing model tied to API usage, offering scalable costs aligned with organizational size and threat data volume. While potentially more cost-effective for organizations seeking to reduce infrastructure overhead, integration and training investments must also be considered.
Automation and Orchestration Capabilities
While Cortex XSOAR is renowned for its mature SOAR capabilities, GPT-5.4-Cyber integrates AI-driven automated playbooks that dynamically adapt based on threat context, enabling proactive and autonomous threat hunting and response. This contrasts with the more static automation workflows of traditional platforms, which often require manual tuning.
Furthermore, GPT-5.4-Cyber’s explainability modules facilitate human-in-the-loop interactions, blending automation with analyst oversight to balance speed and accuracy.
Integration and Ecosystem Flexibility
GPT-5.4-Cyber is designed with an API-first architecture, supporting modular connectors that integrate with existing SIEMs, endpoint detection tools, and threat intelligence platforms. This flexibility allows organizations to augment rather than replace existing security stacks, easing adoption hurdles. Traditional platforms boast extensive app ecosystems but may lack the agile adaptability inherent in GPT-5.4-Cyber’s design.
Implementation Roadmap: Deploying GPT-5.4-Cyber in Your Security Operations Center
Successfully integrating GPT-5.4-Cyber into a Security Operations Center (SOC) requires careful planning and execution. The following roadmap outlines a comprehensive 90-day deployment plan, from prerequisites to team training, ensuring optimal alignment with organizational security objectives.
Prerequisites and Initial Assessment
Before deployment, organizations should conduct a thorough readiness assessment covering:
- Infrastructure Evaluation: Ensure sufficient compute resources, especially GPU-enabled servers or cloud environments supporting low-latency AI inference.
- Data Availability: Validate access to relevant threat intelligence feeds, log sources, and telemetry data necessary for effective model ingestion.
- Security Posture Review: Map existing security tools and workflows to identify integration points and potential gaps the model can address.
- Compliance and Privacy: Confirm that data handling aligns with organizational policy and regulatory requirements.
Network Architecture Changes
GPT-5.4-Cyber deployment may necessitate modifications to network architecture to facilitate secure data flow:
- API Gateway Implementation: Deploy secure API gateways to manage communication between the model and existing platforms.
- Data Ingestion Pipelines: Establish automated pipelines for real-time feed normalization and forwarding.
- Segmentation and Access Controls: Define network segments for AI inference workloads to enforce least-privilege access.
- Latency Optimization: Position inference engines close to data sources or leverage edge computing to minimize processing delays.
API Integration Patterns
Seamless interoperability with existing SOC tools is facilitated through well-defined API integration:
- Push and Pull Models: Utilize push APIs for streaming threat data to GPT-5.4-Cyber and pull APIs for retrieving analysis and alerts.
- Webhook Support: Configure webhooks to enable event-driven workflows and alert notifications.
- Bidirectional Communication: Enable feedback loops allowing SOC analysts to provide input, improving model accuracy over time.
- Connector Development: Develop custom connectors as needed for proprietary or legacy systems.
Team Training and Change Management
Adoption success hinges on empowering SOC personnel with the knowledge and skills to leverage GPT-5.4-Cyber effectively:
- Technical Training: Provide hands-on workshops covering API usage, dashboard interpretation, and alert triage.
- AI Literacy: Educate teams on AI concepts, model explainability, and limitations to foster trust and appropriate reliance.
- Process Reengineering: Update incident response playbooks to incorporate AI-generated insights and automated actions.
- Continuous Learning: Establish feedback mechanisms to capture analyst experiences and iteratively refine deployment.
90-Day Rollout Timeline
- Days 1-15: Conduct infrastructure readiness checks, finalize procurement, and initiate network architecture modifications.
- Days 16-30: Integrate threat feeds, deploy API gateways, and configure data ingestion pipelines.
- Days 31-45: Pilot GPT-5.4-Cyber inference on shadow SOC data streams, validate detection outputs, and tune model parameters.
- Days 46-60: Begin phased integration with existing SIEM/SOAR platforms, conduct team training sessions, and update operational processes.
- Days 61-75: Expand model usage to live incident response, monitor performance metrics, and optimize alert handling.
- Days 76-90: Complete full deployment, establish continuous improvement cycles, and formalize AI governance policies.
By adhering to this structured roadmap, organizations can minimize risks and accelerate the realization of GPT-5.4-Cyber’s transformative capabilities within their cybersecurity operations.
Expert Perspectives and Industry Reactions
The launch of GPT-5.4-Cyber has elicited a broad spectrum of reactions from cybersecurity experts, Chief Information Security Officers (CISOs), and industry analysts. This section synthesizes these perspectives, highlighting the promise and challenges associated with integrating advanced AI models into security contexts, as well as addressing concerns related to AI safety and ethical use.
Positive Outlook: Enhancing SOC Efficiency and Threat Detection
Many industry leaders have hailed GPT-5.4-Cyber as a watershed moment in cybersecurity technology. Experts emphasize the model’s potential to drastically improve detection rates while reducing analyst workload through intelligent automation and contextual threat understanding.
“GPT-5.4-Cyber’s ability to synthesize disparate threat feeds and provide explainable alerts represents a significant leap forward,” notes Dr. Elena Ramirez, Chief Scientist at CyberDefence Analytics. “It empowers SOC teams to focus on high-impact threats rather than sifting through noise, enhancing both speed and accuracy.”
CISOs from multinational corporations have expressed optimism about the model’s adaptability to diverse environments and its capacity to integrate with existing security architectures without wholesale replacement. This flexibility is viewed as critical for accelerating AI adoption in mature security programs.
Cautious Voices: Addressing AI Safety and Operational Risks
Despite widespread enthusiasm, some experts urge caution regarding the deployment of advanced AI in security operations. Concerns center on model biases, overreliance on automated decisions, and the potential for adversarial manipulation.
“While GPT-5.4-Cyber showcases impressive capabilities, organizations must rigorously validate model outputs and maintain human oversight,” warns Marcus Li, a cybersecurity risk consultant. “AI safety in security contexts demands robust governance frameworks to mitigate false positives, adversarial exploitation, and inadvertent escalation of threats.”
Industry analysts highlight the importance of transparency and explainability, noting that black-box AI models can undermine trust and complicate incident investigations. GPT-5.4-Cyber’s built-in explainability features have been positively received but remain an area for continuous improvement.
Impact on Cybersecurity Workforce and Skillsets
The introduction of GPT-5.4-Cyber also prompts reflection on the evolving role of cybersecurity professionals. Experts advocate for proactive upskilling to equip analysts with AI literacy and data science competencies.
“The model will not replace human analysts but augment their capabilities,” explains Ananya Singh, Director of Security Operations at a leading financial institution. “Training programs must emphasize collaboration between AI and humans, focusing on interpreting AI insights, validating alerts, and managing complex incidents.”
Several organizations have already begun integrating GPT-5.4-Cyber into SOC training curricula, fostering a culture of innovation and continuous learning.
Industry Analyst Assessments and Future Outlook
Leading cybersecurity market analysts have incorporated GPT-5.4-Cyber into their trend forecasts, predicting accelerated adoption of AI-driven threat intelligence solutions over the next 3 to 5 years. Reports underscore the model’s potential to disrupt traditional SIEM and SOAR paradigms by offering unified, AI-enhanced visibility and response capabilities.
However, analysts also stress the importance of ecosystem collaboration, recommending that OpenAI and partners continue expanding integrations and community-driven improvements. The model’s success will depend not only on technical excellence but also on addressing operational realities and ethical considerations.
In conclusion, GPT-5.4-Cyber is widely regarded as a transformative innovation with the capacity to reshape cybersecurity operations. Its deployment marks a critical step in the maturation of AI-assisted defense, blending cutting-edge technology with pragmatic security needs and human expertise.