Residential proxies are one of the most misunderstood tools in modern web development.
Some developers associate them only with scraping, others think they are a niche security trick, and many simply avoid them because the terminology sounds complex.
In reality, residential proxies are a practical infrastructure component that solves real engineering problems related to access, reliability, testing, and data collection.
If you build applications that interact with the public internet, understanding how residential proxies work can help you design systems that behave more like real users and less like automated scripts.
This article explains residential proxies from a developer’s perspective. We will focus on how they function, where they fit into real workflows, and what trade-offs you should evaluate before integrating them into your stack.
What Residential Proxies Actually Are
A residential proxy routes your internet traffic through an IP address assigned to a real household device by an internet service provider. When your application sends a request through such a proxy, the target website sees the request as coming from a normal residential user instead of a data center server.
This difference matters because modern websites treat traffic differently depending on its origin. Data center IP addresses are easy to detect because they come from known cloud providers. Residential IPs, on the other hand, blend into normal consumer traffic patterns. From a technical perspective, this means requests routed through residential proxies often face fewer automated restrictions.
For developers, the key idea is that residential proxies do not change what your application sends. They change how your traffic appears to the outside world. Your HTTP requests, headers, and logic remain the same, but the network identity changes.
Why Developers Use Residential Proxies
Most developers first encounter residential proxies when dealing with rate limits or access restrictions.
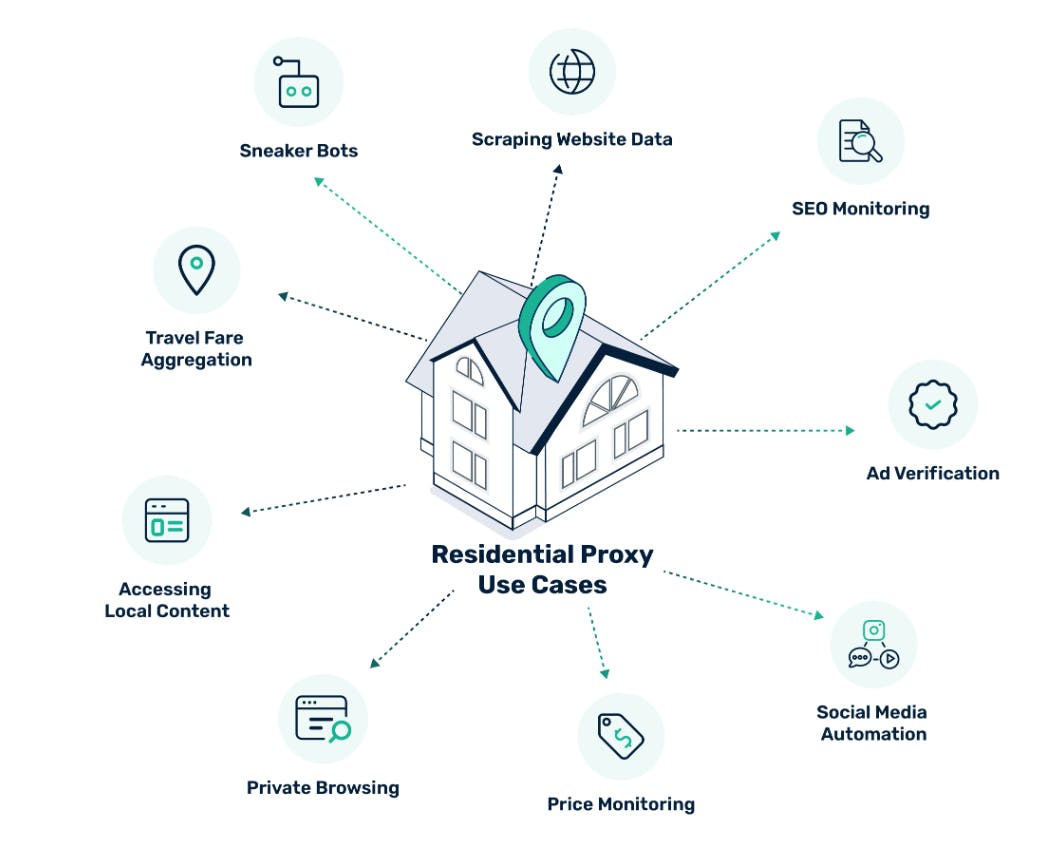
However, the real value goes beyond bypassing blocks. Residential proxies allow developers to simulate geographic diversity, test localized experiences, and collect data under conditions closer to real user behavior.
Consider a product that displays different content based on region. Testing this from a single server location gives incomplete results. Routing requests through residential proxies in different countries allows engineers to validate localization logic without physically moving infrastructure.
Another common use case involves reliability. While VPNs are reliable, some websites aggressively filter traffic that looks automated. If your application depends on public data or external integrations, residential proxies can reduce failure rates by lowering the chance of requests being flagged.
There is also a testing angle. Security teams use residential proxies to verify how their systems respond to real-world traffic patterns. QA engineers use them to test anti-bot logic and geolocation-based flows. In these scenarios, proxies are less about avoidance and more about realism.
How Residential Proxies Work Under the Hood
From a networking standpoint, residential proxy providers maintain large pools of IP addresses sourced from consumer devices. Your application connects to the provider’s gateway, and the gateway routes requests through one of these residential endpoints.
Some systems use rotating sessions, where each request gets a different IP. Others allow sticky sessions, meaning you keep the same IP for a period of time. The choice depends on your use case. Data collection tasks often benefit from rotation, while workflows requiring authentication may need session consistency.
Latency is an important technical detail. Residential routes are generally slower than data center proxies because traffic travels through consumer networks rather than optimized server infrastructure. Developers should account for this by adjusting timeout values and retry logic.
Authentication typically happens through username and password or IP whitelisting. In code, integration usually involves configuring an HTTP client to use the proxy endpoint. The complexity lies less in setup and more in managing sessions, failures, and cost.
Residential vs Data Center Proxies
Understanding the difference between residential and data center proxies helps you choose the right tool. Data center proxies are fast, cheap, and stable. They work well when speed matters more than authenticity. Residential proxies are slower and more expensive but provide higher trust from target websites.
From an engineering perspective, this is a classic trade-off between performance and realism. If you are running internal automation or interacting with APIs designed for machines, data center proxies may be sufficient. If you need traffic to look like genuine user activity, residential proxies become valuable.
Many mature systems combine both. Developers often use data center proxies for bulk operations and switch to residential proxies only when necessary. This hybrid strategy keeps costs manageable while maintaining reliability where it matters.
Common Integration Patterns
Most integrations begin with a simple HTTP client configuration. Developers add proxy credentials, test connectivity, and start routing requests. But production usage usually evolves into a more structured architecture.
A common pattern is building a proxy abstraction layer. Instead of embedding proxy logic throughout the codebase, requests pass through a centralized component that manages selection, rotation, and retries. This makes it easier to swap providers or adjust policies without touching application logic.
Another pattern involves adaptive routing. Systems monitor response codes and automatically switch between proxy types based on failure rates. For example, repeated 403 responses might trigger a shift from data center to residential endpoints.
Logging is critical. Proxy failures can look like application bugs if you lack visibility. Developers should track latency, success rates, and IP rotation behavior to diagnose issues quickly.
Ethical and Legal Considerations
Residential proxies sit in a gray area for many developers because their misuse can create ethical problems. The technology itself is neutral, but how you use it matters. Responsible use means respecting terms of service, avoiding abusive traffic patterns, and ensuring that data collection complies with legal frameworks.
Developers should also understand how proxy providers source their IP addresses. Reputable providers rely on explicit user consent, often through opt-in networks. Choosing transparent providers reduces risk and aligns your infrastructure with ethical standards.
From a practical standpoint, your engineering decisions should assume accountability. If your system sends thousands of requests through residential IPs, you still own the behavior of that traffic. Good rate limiting and respectful crawling practices are part of professional engineering.
Performance and Cost Trade-Offs
Residential proxies are rarely the cheapest option. Pricing usually depends on bandwidth usage, which means inefficient request design can become expensive quickly. Developers should optimize payload size, reduce redundant requests, and cache results where possible.
Performance tuning also becomes important. Because residential networks vary in quality, response times can fluctuate. Implementing smart retry strategies and circuit breakers helps maintain stability.
Some teams underestimate the operational complexity. Proxy pools can change, sessions can expire, and endpoints may occasionally fail. Treat proxy infrastructure like any external dependency and design for resilience rather than assuming perfect uptime.
Security Implications for Developers
Using residential proxies introduces additional security considerations. Since traffic passes through third-party infrastructure, sensitive data should always be encrypted. HTTPS is essential, and credentials should never be exposed in logs or client-side code.
Developers should also isolate proxy usage from core systems when possible. Running proxy-enabled tasks in separate services reduces blast radius if something goes wrong. Monitoring outbound traffic is another good practice, especially in environments where compliance matters.
Authentication management deserves attention as well. Rotating credentials and limiting access scope helps prevent accidental misuse.
When You Should Not Use Residential Proxies
Not every problem requires residential proxies. If an official API exists, it is almost always the better choice. APIs provide stability, clear terms, and predictable performance. Proxies should not be a shortcut around proper integrations.
They are also unnecessary for many internal tools. Developers sometimes adopt proxies too early without validating whether simpler solutions could work. Before adding them, ask whether the problem is truly about network identity or if better request design could solve it.
Complexity has a cost. Every additional dependency increases maintenance overhead, and residential proxies are no exception.
Practical Advice for Getting Started
Start small. Test with a limited workload before scaling. Measure success rates and latency to understand real-world performance. Avoid designing your system around assumptions from provider marketing pages.
Build observability early. Metrics around request outcomes, proxy health, and bandwidth usage will save time later. Treat proxies as infrastructure, not a quick hack.
Finally, design your architecture so proxies are optional rather than mandatory. This flexibility allows you to adjust strategy as requirements change.
Conclusion
Residential proxies are not magic tools, but they are powerful when used correctly. For developers, their real value lies in enabling applications to interact with the internet under realistic conditions. They help with localization testing, reliability, and access challenges that traditional server infrastructure sometimes struggles to handle.
The key is to approach them as an engineering decision rather than a shortcut. Understand the trade-offs, build with observability, and use them responsibly. When integrated thoughtfully, residential proxies become another reliable component in a modern developer’s toolkit, helping you build systems that behave more like real users and less like isolated machines.