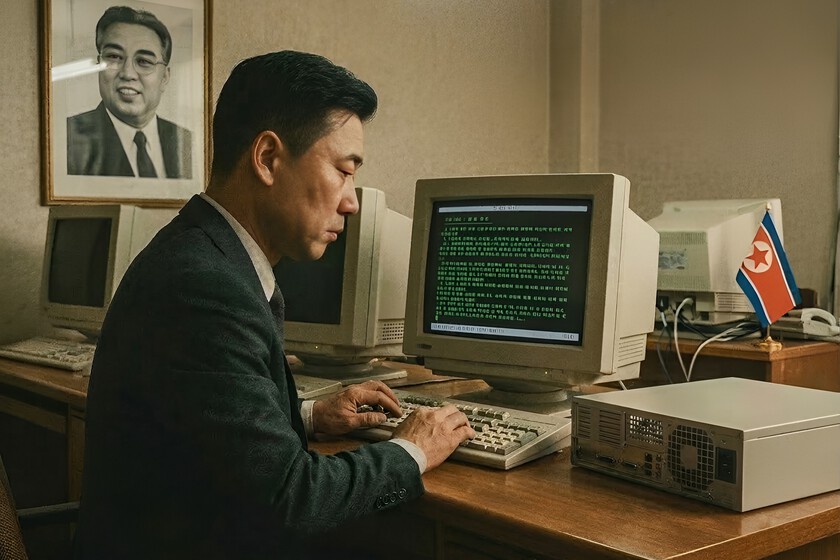
A European company publishes an offer for a remote technological position and, after several filters, hires a candidate who perfectly fits the profile. The resume is solid, the interviews are carried out without problems and, on paper, this incorporation becomes integrated into the team as one more. But there is a possibility that until recently many companies did not even consider: that this worker is not who they say they are. Cybersecurity experts maintain that this phenomenon comes almost exclusively from North Korea, a practice documented in the United States and whose first signs are also beginning to be seen in Europe.
The problem of fake employees in Europe. To understand why it is now starting to cause concern in this part of the world, it is worth first looking at what has already happened in the North American country. There, authorities and cybersecurity specialists have been investigating a very specific pattern for years: supposed technology professionals who were actually part of networks linked to Pyongyang. According to data from the Department of Justice, these operations managed to infiltrate more than 300 companies between 2020 and 2024, generating at least $6.8 million in income for the North Korean country.
How deception works. The process usually begins with building a compelling professional identity. According to the Financial Times, operatives can take over inactive LinkedIn accounts or even pay their owners to use them, and from there create apparently legitimate profiles with falsified resumes and recommendations generated by other members of the network. Language models also help them create culturally appropriate names, plausible email addresses, and messages that reduce linguistic or cultural cues that could previously give them away. In the interview phase, technology plays an increasingly important role: these networks can resort to digital masks, avatars or video filters, and when some companies tighten controls, they also go so far as to pay real intermediaries to appear on video calls in their place.
The success of this scheme is not explained only by the technological tools used by false candidates. It also has to do with a structural weakness within many organizations. According to cybersecurity experts cited by the aforementioned newspaper, the hiring process has rarely been considered a corporate security front. For years it has been managed mainly from human resources, with controls designed to evaluate talent, not to detect infiltration operations. That approach has left a vulnerability that these networks are exploiting.
Once inside the company. Getting through the hiring process is only the first phase of the operation. Some of these schemes include intercepting the laptops that companies send to their new employees to work remotely. After accessing the equipment, operatives can connect from other locations and carry out their work activity using tools based on language models and chatbots. This system allows them to fulfill the tasks assigned by the company and, in some cases, manage several technological jobs at the same time. Furthermore, the risk is not limited to collecting salaries; some also steal information or infect systems with malware.
For threat analysts, the first signs of expansion towards Europe are already visible. According to information collected by the Financial Times, researchers have identified signs that networks linked to North Korea are trying to reproduce in the region the same model that was previously observed in the North American country. One of the elements that has attracted attention is the appearance in the United Kingdom of the so-called laptop farmsspaces where remotely connected laptops are concentrated so that operatives can work as if they were physically in the country. This type of infrastructure suggests that the scheme could also be beginning to be replicated in Europe.
Images | WorldOfSoftware with Nano Banana
In WorldOfSoftware | We knew that North Korea has been infiltrating workers into Western companies for years. Now we know how they do it