Intel Xeon Features To Be Supported By Ubuntu 26.04 LTS – Some Lacking User-Space Packages
Canonical engineer Serkan Uygungelen published a post outlining some of the Intel Xeon CPU features to be supported by the…
A Tragic Science of Beauty | HackerNoon
:::info Astounding Stories of Super-Science October, 1994, by Astounding Stories is part of HackerNoon’s Book Blog Post series. You can…
NetBSD 11.0-RC2 Released For Testing
The big NetBSD 11.0 release continues on approach with NetBSD 11.0-RC2 having been released as the latest test candidate. NetBSD…
Chukwuemeka Afigbo on why Africa’s deep tech moment is now
Chukwuemeka Afigbo is making a long-term bet: Africa’s most ambitious technologists are not constrained by a shortage of ideas, but…
The Corruption Behind the Pall | HackerNoon
:::info Astounding Stories of Super-Science October, 1994, by Astounding Stories is part of HackerNoon’s Book Blog Post series. You can…
Oracle Updates Free Solaris CBE For Open-Source Developers / Non-Production Uses
Four years ago Oracle announced Solaris CBE as the "Common Build Environment" version of Solaris 11.4. Oracle Solaris CBE is…
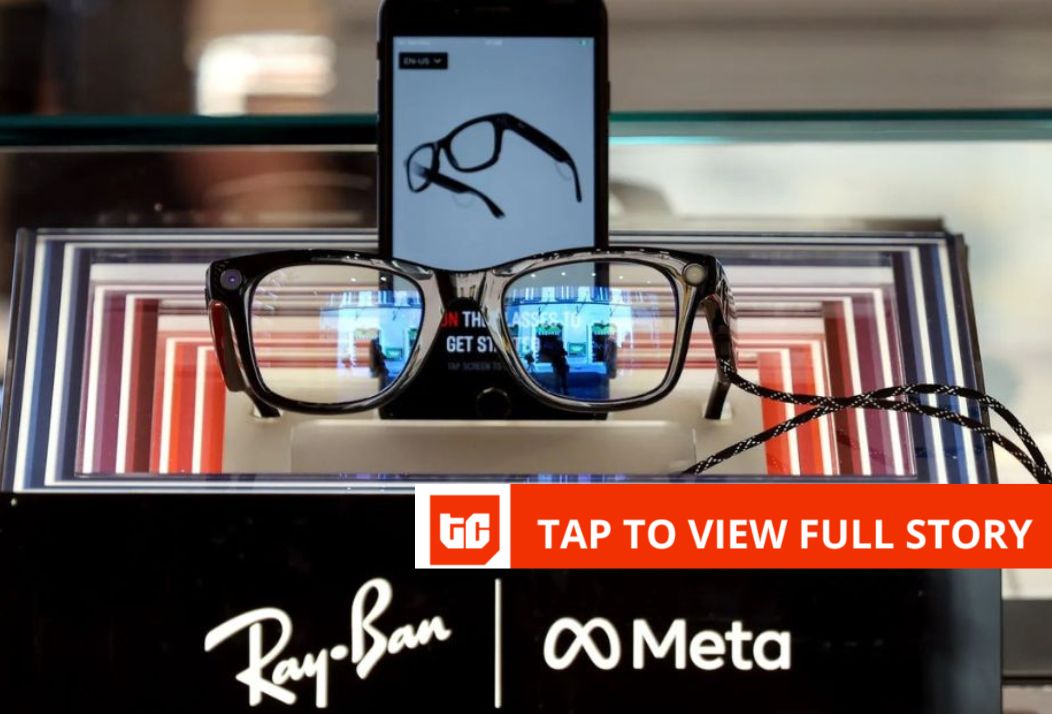
Kenya’s data regulator asked to probe Meta’s smart glasses footage
The Oversight Labs, a Kenyan digital rights group, has asked the Office of the Data Protection Commissioner (ODPC) to investigate…
How to Turn a Blog Into a Book (Publish-Ready in No Time)
If you’ve been blogging for a while, you probably have dozens (or even hundreds) of posts sitting on your site.…
United One — The Place Where Belonging Becomes Power | HackerNoon
You already sense it. The headlines talk about crypto rallies and AI breakthroughs, and part of you knows this is…
Iran-Linked MuddyWater Hackers Target U.S. Networks With New Dindoor Backdoor
New research from Broadcom's Symantec and Carbon Black Threat Hunter Team has discovered evidence of an Iranian hacking group embedding…