Claude Code Source Code Leak: An In-Depth Analysis of the 2026 Security Incident

By Markos Symeonides
On March 31, 2026, the AI industry was shaken by a significant security incident involving Anthropic’s flagship developer tool, Claude Code. Version 2.1.88 of Claude Code was released with a critical packaging error that exposed approximately 2,000 source code files, totaling over 512,000 lines of code. This leak came just days after a previous exposure, marking a turbulent week for the startup known for its cautious approach to AI development.
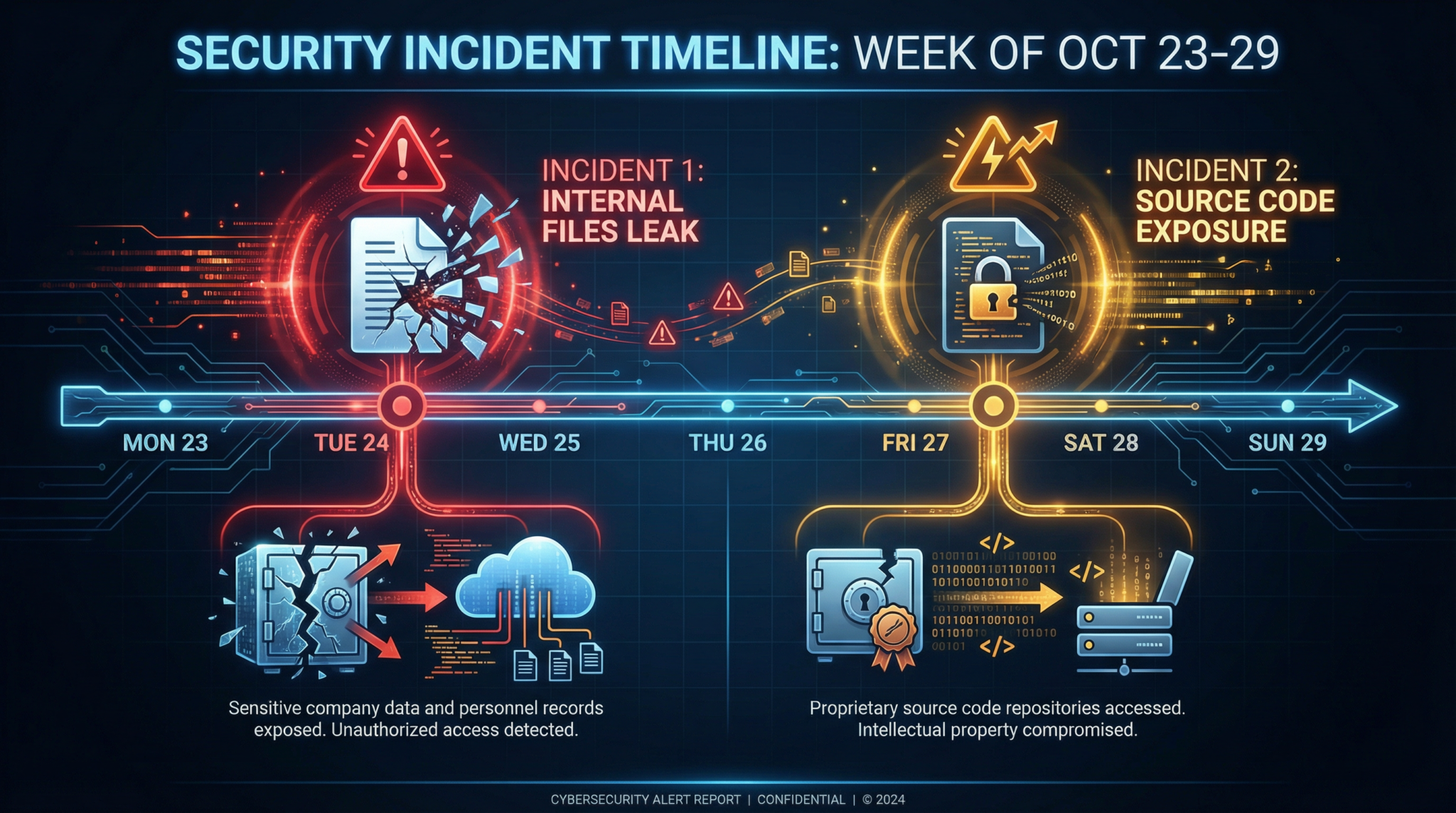
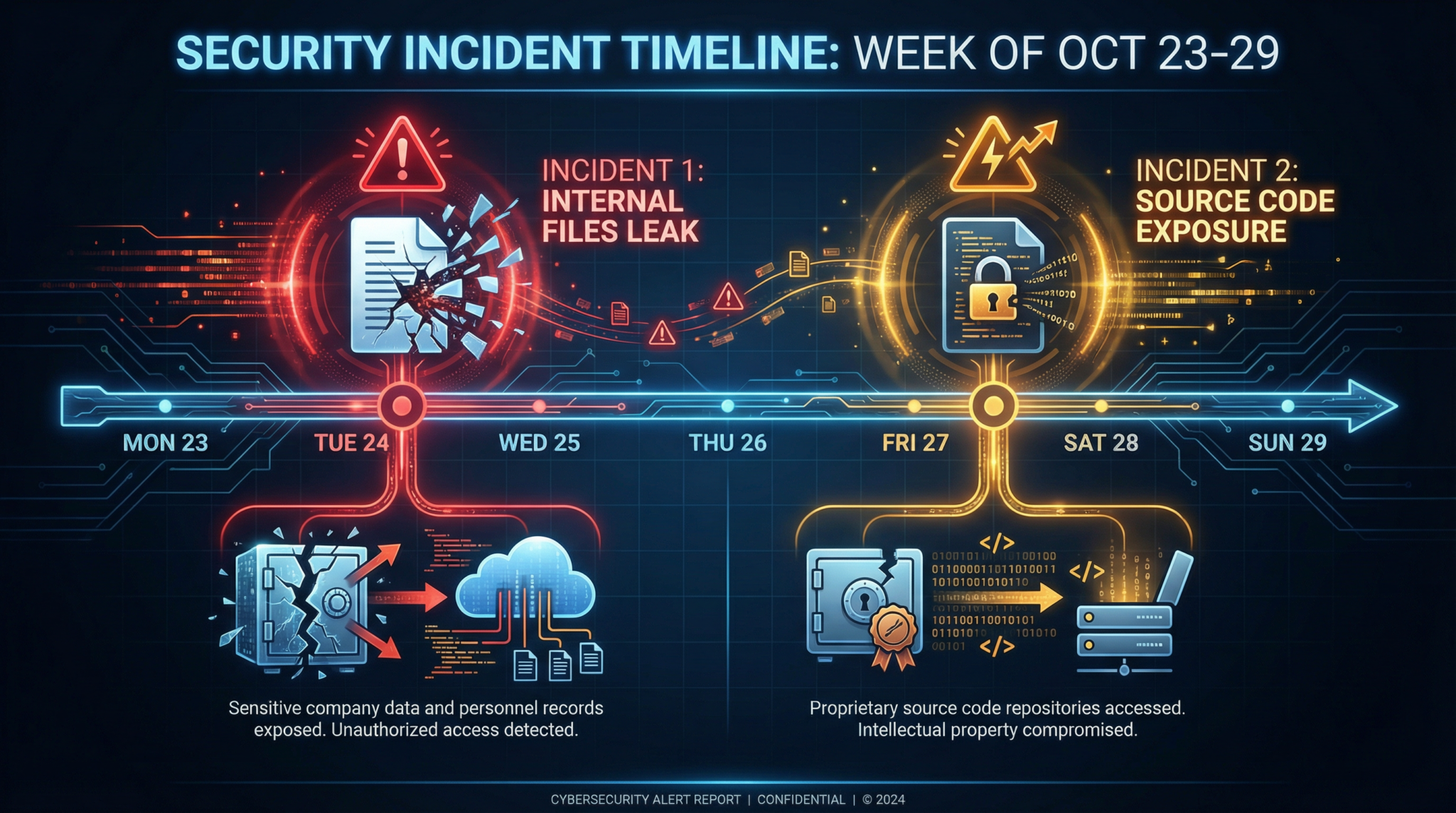
1. Timeline of Both Leaks: A Week of Unintended Disclosures
The chain of events began on March 27, 2026, when Anthropic inadvertently exposed roughly 3,000 internal files. This initial leak included sensitive project documents, such as a draft blog post detailing the unreleased “Mythos” model — a next-gen AI system that had garnered significant anticipation within the community. Though the AI model weights or datasets were not compromised, the exposure of internal planning documents raised eyebrows about Anthropic’s operational security.
Just four days later, on March 31, Anthropic pushed an update to Claude Code version 2.1.88. However, this release contained a critical packaging error that led to the accidental inclusion of the tool’s source code — approximately 2,000 files and over half a million lines of code. Security researcher Chaofan Shou was quick to discover the leak and promptly announced it on the social media platform X, bringing immediate attention to the issue.
Anthropic responded swiftly, clarifying that the incident was a “release packaging issue caused by human error, not a security breach,” emphasizing that no outsiders had actively infiltrated their systems. Despite this reassurance, the back-to-back leaks raised serious questions about Anthropic’s internal security protocols and quality assurance processes.
2. What Was Actually Exposed — And What Was Not
Contrary to some initial speculation, the leaked files did not include the Claude AI model weights or training data. Instead, the exposed material contained the software scaffolding that powers Claude Code’s behavior — the instructions that govern how the AI interacts with tools, executes commands, and enforces operational constraints.
This software scaffolding includes:
- Command parsing and execution frameworks
- Interfaces to third-party APIs and internal tools
- Behavioral guidelines and safety limiters
- Logging and telemetry components
- Developer tools and debugging utilities
In other words, the leak revealed the underlying infrastructure that orchestrates Claude Code’s interactions, rather than the AI’s neural network or training corpus. This distinction is crucial: while the AI model itself remains proprietary and secure, the leaked code provides unprecedented insight into the architecture and operational design that make Claude Code a powerful developer platform.
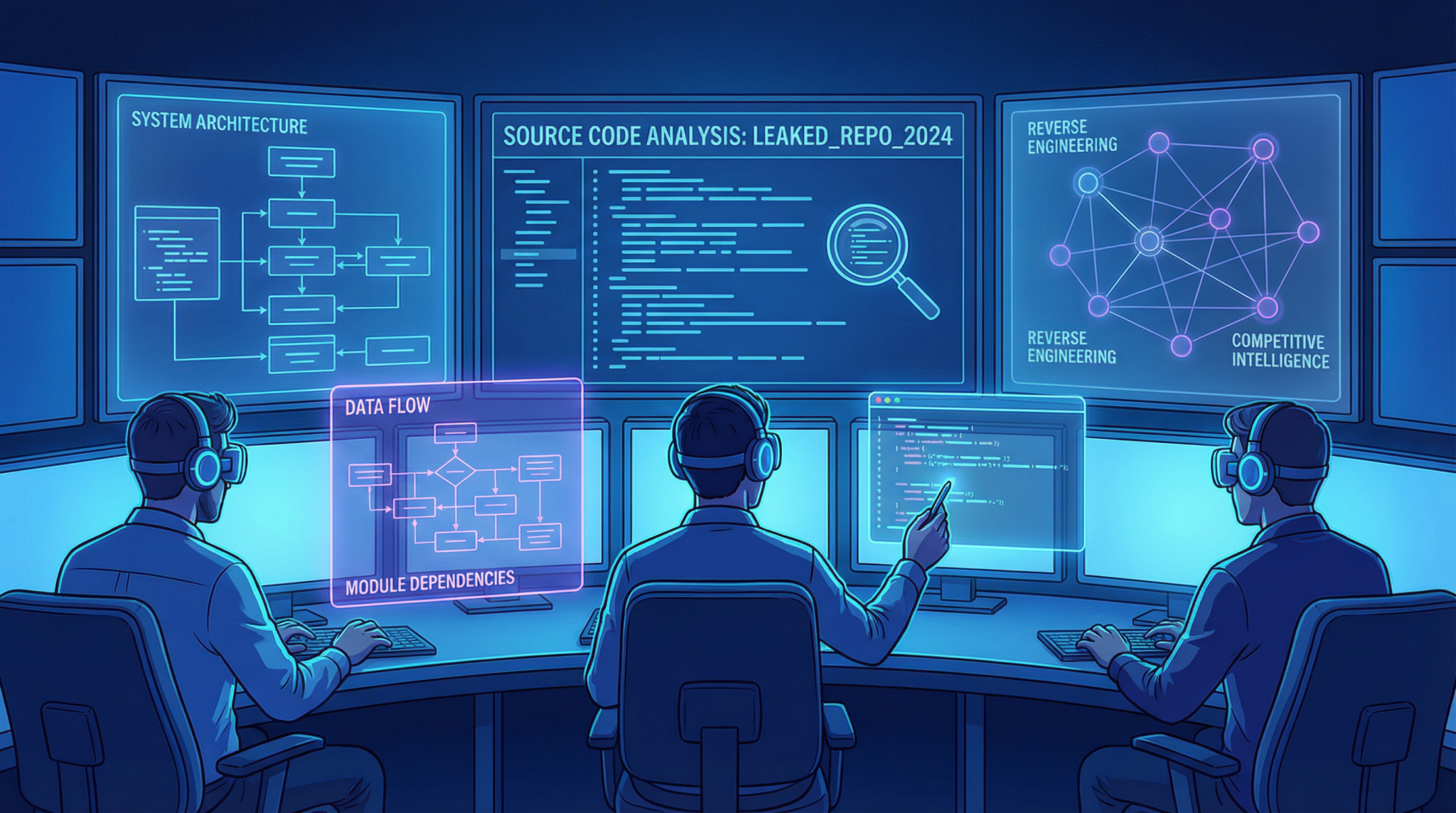
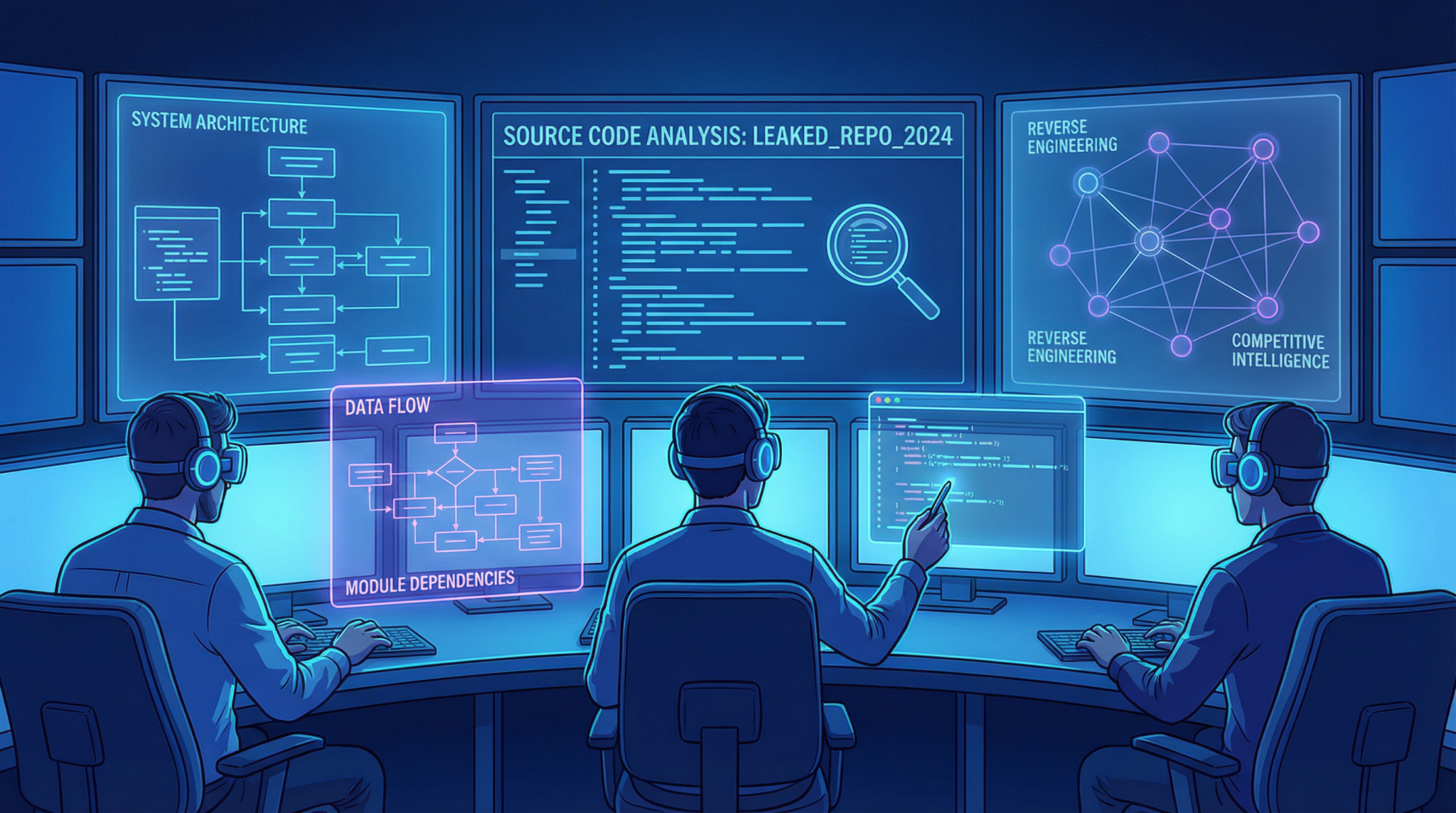
3. Technical Analysis: What Developers Discovered in the Leak
Developers and security experts who sifted through the leaked source code quickly recognized that Claude Code embodies a production-grade developer experience, far beyond a simple API wrapper. The software offers robust integration with a wide variety of tools and services, featuring:
- Modular plugin architectures that enable seamless extension of capabilities
- Fine-grained control structures allowing developers to specify nuanced AI behavior
- Embedded safety checks to prevent unsafe or unintended operations
- Rich telemetry and debugging interfaces designed for iterative development
One developer remarked that the leak showcased Claude Code as “a sophisticated orchestration layer” that manages not only AI calls but also how the AI interacts with the external environment and the developer’s workflow. The code reveals a deliberate design philosophy that emphasizes reliability, extensibility, and control.
The exposure of these components offers a rare opportunity for competitors and third-party developers to study the inner workings of one of today’s most advanced AI developer tools. It also highlights Anthropic’s commitment to building a comprehensive and developer-friendly platform rather than a bare-bones interface.
4. Competitive Implications: Lessons for Rivals and the Industry
Claude Code’s source leak provides a unique vantage point for competitors, including OpenAI and emerging AI startups. While the model itself remains undisclosed, the scaffolding’s design reveals how Anthropic has differentiated its offering by investing heavily in the developer experience and operational safety.
OpenAI’s decision to shut down its own tool, Sora, in order to refocus resources on competing with Claude Code underscores the competitive pressure Anthropic has created. Fidji Simo, OpenAI’s head of product, described Claude Code’s success as an internal “wake-up call,” prompting a reassessment of how AI tools are architected and delivered.
Industry players can glean several strategic lessons from the leak and its aftermath:
- Developer Experience Matters: Robust scaffolding and extensibility can be as critical as raw AI capabilities.
- Safety Mechanisms are Integral: Embedding operational limits and safety checks within tooling is essential in production environments.
- Rapid Innovation Requires Rigorous Security: As competition accelerates, companies must balance speed with airtight release processes.
- Transparency and Responsiveness: Prompt acknowledgment and clear communication during incidents can mitigate reputational damage.
For the AI developer tools market, these insights will likely spur increased investment in integrated tooling and security-focused development workflows.
5. Anthropic’s Identity as the “Careful AI Company” Under Scrutiny
Anthropic has cultivated a reputation as the “careful AI company,” emphasizing ethics, safety, and transparency in AI development. Founded by former OpenAI researchers, Anthropic positioned itself as a counterbalance to perceived recklessness in the AI race.
However, the dual leaks within one week have put this identity to the test. Security experts and industry observers have expressed concern about how a company so focused on safety could experience such operational lapses. While Anthropic maintains that these were human errors rather than malicious breaches, the incidents reveal potential weaknesses in internal processes, especially in release management.
Anthropic’s CEO and security teams have reportedly initiated comprehensive reviews of their release pipelines and enhanced automation to prevent similar mistakes. The company’s response highlights the tension between rapid product iteration and robust security — a challenge that AI companies of all sizes face.
Top 5 Advances in Model Optimization for AI Hardware explores how companies balance innovation with risk mitigation in rapidly evolving AI ecosystems, a topic directly relevant to Anthropic’s current challenges.
6. Impact on the AI Developer Tools Market
The Claude Code leaks have rippled through the AI developer tools market, raising awareness about the complexity and value of the software scaffolding that supports AI applications. More than ever, enterprises and developers recognize that AI tools are not just about model performance but also about how effectively those models can be integrated, controlled, and audited.
Claude Code’s comprehensive feature set, as revealed through the leaked code, has set a new benchmark for what developers expect from AI tooling. This drives competitors to enhance their platforms with improved modularity, safety features, and user experience improvements.
Simultaneously, the leaks have prompted enterprises to scrutinize the security practices of AI vendors more closely. Procurement teams are increasingly demanding transparency around code management, release procedures, and incident response capabilities when selecting AI developer tools.
7. Security Lessons for AI Companies
The dual leaks at Anthropic serve as a cautionary tale for all AI companies about the critical importance of operational security and release governance. Key takeaways include:
- Automate Packaging and Release Processes: Reducing human error through automation and continuous integration pipelines can prevent accidental exposure of sensitive files.
- Implement Multi-Layered Access Controls: Strict role-based permissions and auditing can limit the risk of accidental leaks during build or deployment.
- Conduct Frequent Security Audits: Regular, comprehensive reviews of release artifacts ensure no unintended files are included.
- Foster a Security-First Culture: Educating teams about the risks and consequences of leaks reinforces vigilance across all departments.
Given the sensitive nature of AI software and the competitive advantage it confers, these lessons are vital as the industry scales. Anthropic’s transparency about the issues and remedial steps sets an example for proactive incident management.
Comprehensive Guide to API Testing in AI Development – November 2023 details practical strategies for preventing leaks and unauthorized access in AI project workflows, complementing the lessons from Anthropic’s experience.
8. What This Means for Claude Code Users
For developers and enterprises relying on Claude Code, the leaks present a nuanced risk profile. While the AI model remains secure, the exposure of the scaffolding code means that some implementation details, safety limiters, and tool integrations are now public knowledge.
This could potentially allow sophisticated users or competitors to reverse-engineer aspects of Claude Code’s behavior or develop imitative features. However, since the core AI model and training data remain confidential, the unique intelligence at Claude’s heart is intact.
Anthropic has assured users that no customer data or deployment secrets were compromised. They have also accelerated updates to patch the packaging process and reinforce operational safeguards. Users are encouraged to update to the latest versions and monitor official channels for security advisories.
Looking forward, the incident highlights the importance of vigilance and prompt response in maintaining trust in AI platforms, especially those underpinning mission-critical applications.
Evolution of AI up to 2026 offers guidance for organizations assessing the security posture of AI platforms like Claude Code, helping users make informed decisions in light of recent events.
Conclusion
The March 2026 Claude Code source code leak represents a pivotal moment in AI development history, illustrating both the promise and pitfalls of building advanced developer-centric AI tools. While Anthropic’s swift acknowledgment and mitigation efforts demonstrate responsible stewardship, the incidents underscore the complexity of securing AI ecosystems amid rapid innovation.
As the AI industry continues to mature, the lessons from Anthropic’s experience will resonate widely: robust security practices, comprehensive developer experiences, and transparent communication are essential pillars for sustainable AI progress. Claude Code remains a formidable player in the AI tooling landscape, but the path forward demands heightened diligence and collaboration across the community.









