In the high-stakes bazaar of the dark web, there is a clear hierarchy of value. A stolen credit card is a mere commodity, often trading for the price of a cup of coffee. A Social Security number is a versatile tool. But a comprehensive medical record? That is a masterpiece. It contains a permanent, unchangeable blueprint of a human life — history, genetic markers, and biometric vulnerabilities. Unlike a compromised bank account, which can be frozen and reset, a leaked genomic sequence or a chronic health history is a permanent exposure.
As the digital landscape shifts in 2026, healthcare security has moved beyond simple data theft into something far more existential. We are witnessing a transition where hospitals are no longer just repositories of data, but front-line targets in a broader geopolitical and economic struggle. The industry is no longer just losing privacy; it is losing the ability to verify identity within the very systems designed to preserve life. When the “Patient Zero” of a cyberattack is no longer a compromised laptop but a corrupted surgical record, the traditional boundaries of cybersecurity dissolve into a matter of public safety.
The Anatomy of a $12.6 Million Breach
For over a decade, healthcare has remained the most expensive sector for cyber incidents. However, 2026 has seen a staggering escalation. Recent industry benchmarks indicate that the average cost of a healthcare data breach has spiked to $12.6 million per incident.
This “triple penalty” isn’t merely a result of technical repair costs. It is a compounding debt driven by three primary factors:
- Regulatory Volatility: With the implementation of more stringent global mandates like NIS2 and updated privacy frameworks, the legal price of a leak has reached record highs.
- The Black-Market Premium: Medical records fetch up to 40 times more than financial data because, unlike a credit card, a person’s DNA and chronic history cannot be “canceled” or “reissued.”
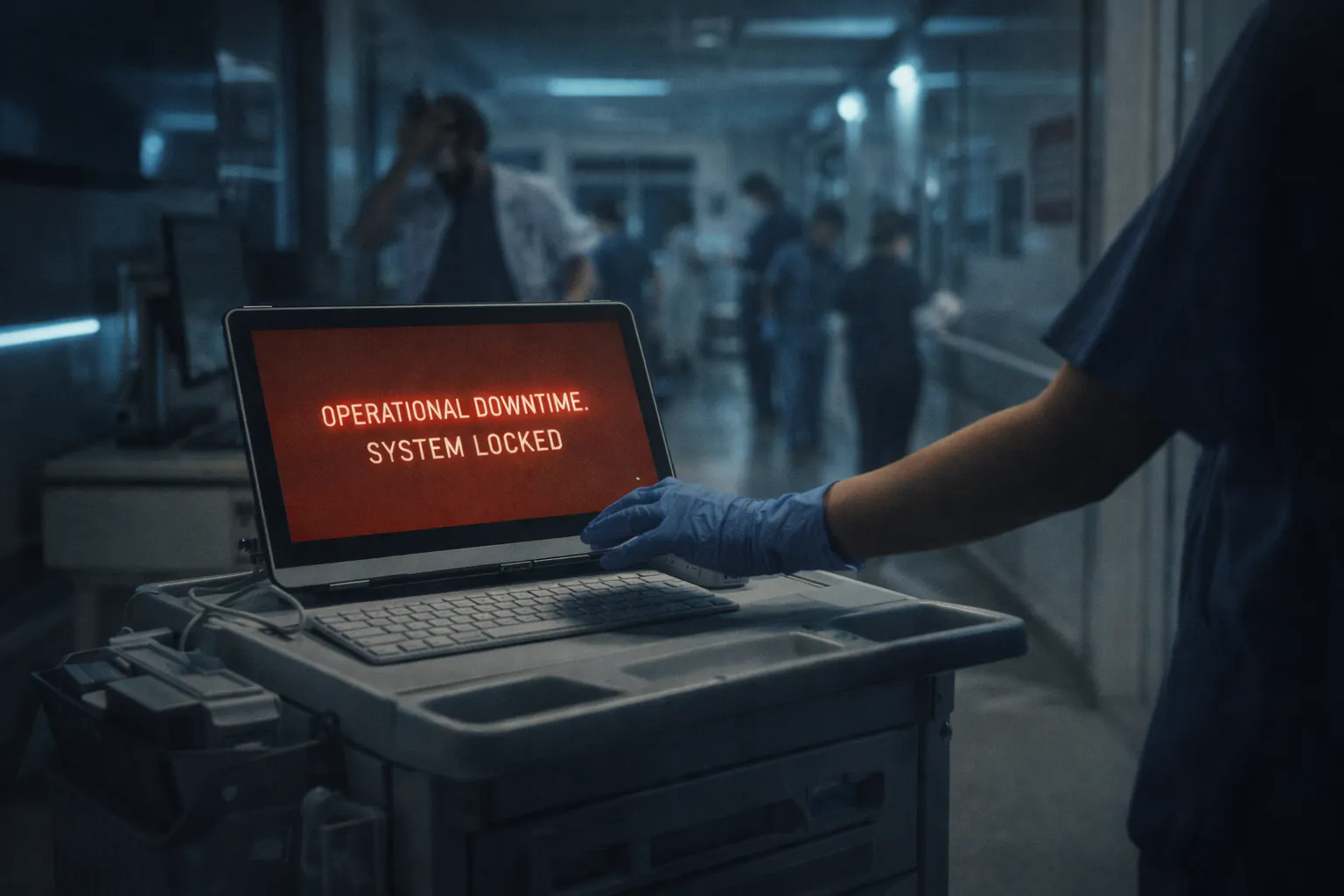
- Operational Paralysis: When a hospital network goes dark, the loss isn’t just financial — it is a disruption of the human supply chain. Diverted ambulances and canceled surgeries create a liability tail that lasts for years.
The financial fallout is significant, but the underlying “Identity Crisis” is what makes these breaches truly dangerous. As analyzed in recent healthcare cybersecurity reporting, the tail of a breach now extends far beyond the initial cleanup, often impacting a provider’s reputation and operational integrity for years.
The Rise of the “Synthetic Patient”
The most terrifying frontier of modern cyber warfare isn’t the theft of existing identities, but the algorithmic creation of new ones. Organizations like the Electronic Frontier Foundation (EFF) have frequently highlighted the vulnerabilities inherent in digital-first healthcare, and 2026 marks the arrival of the Synthetic Patient.
Unlike traditional identity theft, where an attacker assumes the persona of a real person, synthetic fraud involves stitching together real stolen data — such as a child’s Social Security number — with entirely fabricated personas. Powered by Agentic AI, these “ghost patients” now possess plausible medical histories, social media footprints, and deepfaked voice profiles for telehealth verification.
These synthetic identities are bypassing traditional hospital verification systems with ease. The danger isn’t just financial fraud; it is data pollution. When a synthetic identity’s fraudulent allergies or blood types are merged with a real person’s file, the “Patient Zero” of the breach isn’t a server — it’s a human being receiving the wrong clinical treatment.
The Human Cost of “Bit-Rot”
It is easy to discuss cybersecurity in terms of “bits and bytes,” but in the clinical environment, “packet loss” is measured in morbidity rates. Reports often show that a significant percentage of physicians experience delays in critical care — such as prior authorizations or emergency diagnostics — during a cyberattack.
When attackers target biotechnology firms or pharmaceutical chains, they aren’t just looking for research gold; they are looking for leverage. By holding the “digital twin” of a patient’s history hostage, they are effectively locking that patient out of their own future.
“The most expensive data in the world isn’t a credit card, it’s your DNA.”
Hardening the Digital Immune System
To survive an era of $12.6 million breaches and synthetic ghosts, healthcare infrastructure must evolve beyond the “fortress” mentality. A static firewall cannot stop an identity that looks, talks, and “acts” like a legitimate patient.
The industry must shift toward a Zero Trust for Identity framework, prioritizing:
- Cryptographic Identity Verification: Moving away from easily intercepted SMS codes and toward hardware-backed, biometric “proof-of-life.”
- Blockchain-Immutable Records: Ensuring that a patient’s medical history is traceable and cannot be altered by an external intruder or a synthetic persona.
- AI-Driven Anomaly Detection: Utilizing defense-grade AI to spot the machine-speed movements of unauthorized actors within the network.
For those tracking the intersection of technology and risk, the NIST Cybersecurity Framework 2.0 and the HHS 405(d) Aligning Health Care Industry Security Approaches provide a roadmap for navigating these threats.
Conclusion: A Breach of the Self
As we continue to weave our biological lives into the digital tapestry, it is vital to recognize that the healthcare industry is facing a crisis of trust as much as a crisis of technology. We are entering an era where the integrity of a medical database is as critical to public health as the sterility of a surgical suite. When data is manipulated or identities are fabricated at the speed of AI, the consequences ripple outward from the server room to the pharmacy, the laboratory, and ultimately, the bedside.
Protecting healthcare infrastructure in 2026 requires more than just better encryption; it requires a fundamental reimagining of digital identity. To protect the network is, quite literally, to protect the patient. As the boundary between our physical bodies and our digital records continues to dissolve, a breach of data is no longer just a corporate headache or a regulatory hurdle — it is a breach of the self. The path forward lies in building a digital immune system that is as resilient, adaptive, and personal as the biological systems it is designed to safeguard.
Stay informed on the latest shifts in the digital landscape by exploring deep dives on Zero Trust in Clinical Environments.