Private Companies Are Becoming Strategic Targets in Global Cyber Operations
In the shadowed corridors of cyberspace, where digital frontiers stretch beyond the horizon of imagination, a profound transformation has taken root. For much of the past two decades, nation-state cyber operations resembled carefully orchestrated expeditions into the fortress-like domains of government agencies, diplomatic networks, and military systems. Today, that focus has shifted like tectonic plates beneath the digital landscape. Increasingly, private organizations find themselves drawn into the swirling currents of geopolitical cyber activity, their digital territories becoming battlegrounds they never anticipated entering.
Security analysts witness foreign government–linked hacking groups expanding their operations with the methodical precision of explorers charting new continents, now including corporations, infrastructure providers, and technology firms in their vast campaigns. In many cases, these attacks pulse not with the rhythm of financial motivation but instead beat to the drums of intelligence gathering, strategic influence, and economic advantage — a symphony of digital conquest. According to recent assessments by the Cybersecurity and Infrastructure Security Agency (CISA), these actors are increasingly leveraging private sector vulnerabilities to achieve long-term geopolitical goals.
As global economies weave themselves into an ever-more intricate tapestry of digital interconnection, the information flowing through corporate systems has become as precious as the data treasured within government vaults, gleaming like buried gold in the depths of servers and databases.
The Changing Role of Advanced Persistent Threat Groups
Many of the operations attributed to foreign governments unfold through the shadowy work of advanced persistent threat (APT) groups — digital nomads who move through cyberspace with the patience of seasoned hunters. These teams operate with long-term objectives that stretch across seasons and years, attempting to slip silently into networks like morning mist, remaining undetected for extended periods while they harvest their invisible bounty.
Unlike conventional cybercriminals who chase the quick gleam of financial returns, APT actors may spend months or even years nestled deep within compromised systems, gathering information with the methodical care of archaeologists uncovering ancient treasures, piece by digital piece.
Historically, these groups concentrated their efforts heavily on government infrastructure and defense contractors, like explorers focusing on known territories. However, cybersecurity investigations increasingly illuminate campaigns targeting commercial industries, particularly those involved in emerging technologies and critical supply chains — new frontiers rich with untold digital resources. Detailed tracking of APT groups by Mandiant shows a clear pivot toward high-value intellectual property in the private sector.
Industries frequently mentioned in threat intelligence reports paint a portrait of modern strategic value:
- semiconductor manufacturing
- artificial intelligence development
- telecommunications
- energy infrastructure
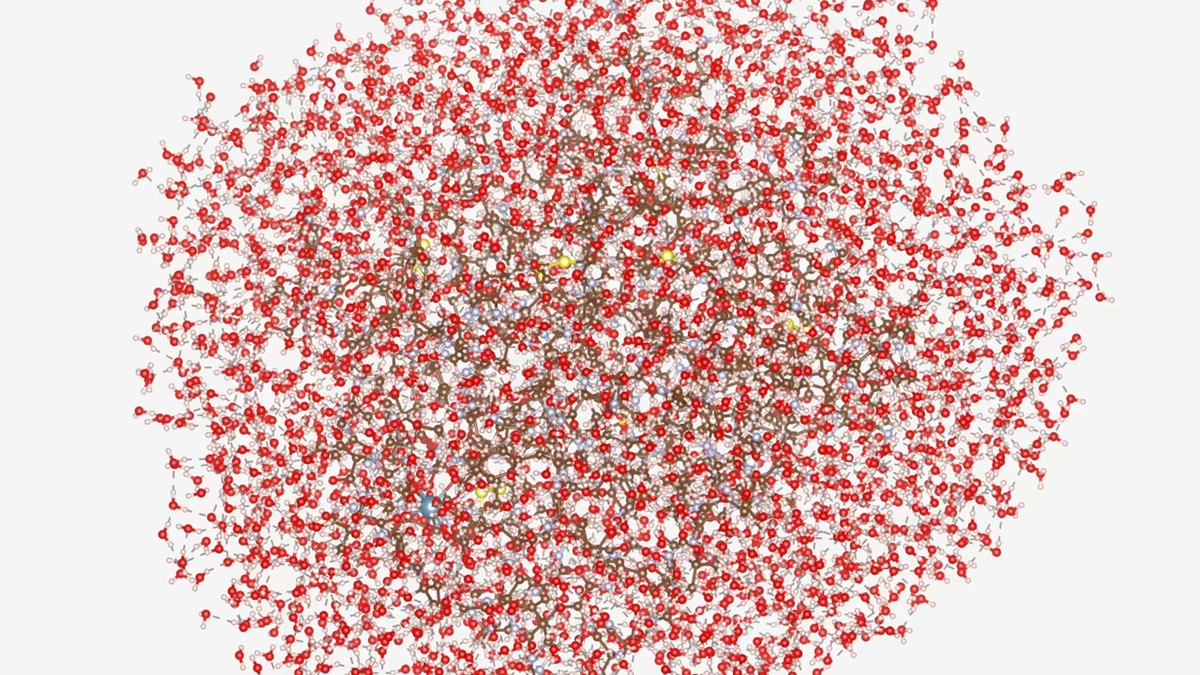
- biotechnology and pharmaceuticals
Access to research data, product designs, and manufacturing processes provides strategic advantages to competing nations, each piece of stolen knowledge becoming a compass pointing toward technological supremacy.
Corporate Networks Offer Valuable Intelligence
Corporate systems now cradle massive repositories of sensitive information that gleam like precious minerals to foreign intelligence services. This digital treasure trove encompasses proprietary technology, internal communications, and insights into market strategies — each byte containing potential power to reshape competitive landscapes.
In some campaigns, attackers focus their efforts on intellectual property theft, mining these digital veins for innovation gold. In others, they seek pathways through supply chains and vendor relationships, each connection offering passage into additional networks like hidden tunnels between underground chambers.
Cybersecurity analysts have observed that compromising a single software vendor or service provider creates cascading effects that ripple across thousands of organizations, much like how disturbing one stone in a mountain stream can alter the entire flow downstream. The breach echoes through digital ecosystems with surprising reach and devastating effect. This “island hopping” strategy is highlighted in CrowdStrike’s Global Threat Report, which notes the efficiency of targeting the supply chain to reach ultimate targets.
The increasing complexity of global technology ecosystems has therefore expanded the constellation of potential entry points for attackers, each connection point sparkling like stars in a vast digital universe, waiting to be discovered by those who know how to navigate these electronic heavens.
Geopolitical Rivalries Are Driving More Cyber Activity
Many experts witness the surge in attacks on private organizations as a reflection of intensifying geopolitical competition, where nations clash not with traditional weapons but through the ethereal battlefields of cyberspace. Areas such as technology, energy, and digital infrastructure have become the new territories to conquer, each domain offering strategic advantages that could tip the balance of global power.
As nations race to develop advanced capabilities in fields like artificial intelligence and semiconductor manufacturing, cyber operations serve as both telescope and excavation tool — gathering intelligence while accelerating domestic innovation efforts. These digital expeditions probe the frontiers of human knowledge, seeking to uncover secrets that could reshape the future.
Tensions between major powers have also contributed to a rising tide of cyber activity targeting sectors tied to national economic priorities, each wave of attacks crashing against digital shores with increasing frequency and force. Reports from the Center for Strategic and International Studies (CSIS) frequently document how trade disputes and regional conflicts manifest as increased digital probing of corporate assets.
While some campaigns unfold with the patient rhythm of long-term espionage, others surge forward in disruptive operations designed to undermine confidence in digital infrastructure, shaking the very foundations upon which our connected world stands.
The Private Sector Is Now Part of the Cyber Battlefield
The expanding scope of nation-state cyber operations means that organizations dwelling far from traditional government or defense sectors can still find themselves swept into this digital maelstrom, their peaceful corporate territories transformed into contested ground.
Companies that nurture cutting-edge technology, operate critical infrastructure, or participate in sensitive supply chains may discover themselves facing heightened risks, like settlements built unknowingly on valuable land that attracts the attention of distant powers.

Even smaller firms find themselves affected when they provide services or components that flow into larger organizational rivers, each tributary potentially leading explorers back to greater prizes.
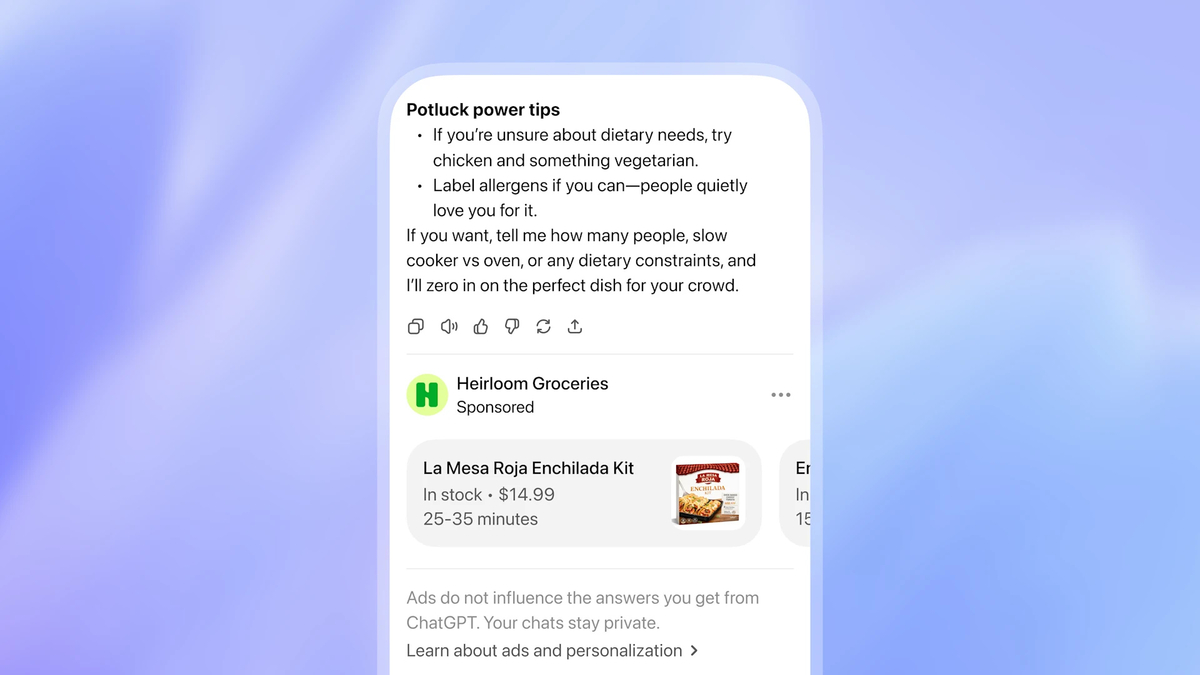
This transformation has compelled many companies to reimagine their cybersecurity strategies, awakening to the reality that they face exposure not only to criminal hackers but also to sophisticated government-backed threat actors — digital armies equipped with resources and patience that dwarf typical criminal enterprises. Organizations are increasingly adopting the NIST Cybersecurity Framework to better align their defenses against these high-resource adversaries.
Preparing for a Broader Threat Landscape
As the digital economy continues its relentless expansion, growing like a vast digital ecosystem, the boundary between national security and corporate cybersecurity dissolves like morning fog, leaving behind a landscape where the two domains merge into one seamless terrain.
Governments, technology firms, and security organizations collaborate to improve threat intelligence sharing and strengthen defenses against sophisticated cyber campaigns, building networks of cooperation that span continents and industries, each alliance adding strength to the collective digital immune system.
For many organizations, the challenge now lies in recognizing that global cyber conflict no longer respects the traditional borders of government networks. In this interconnected digital ecosystem, where data flows like rivers between continents, businesses across a wide spectrum of industries may discover themselves operating on the front lines of geopolitical cyber competition, their servers and databases becoming outposts in an invisible war that shapes the future of global power.
Frequently Asked Questions
What is a nation-state cyberattack?
A nation-state cyberattack represents a sophisticated digital expedition believed to be conducted or supported by a government. These operations unfold through specialized groups that pursue strategic objectives such as intelligence gathering, surveillance, or disruption of critical infrastructure — each attack carefully orchestrated like a military campaign in the invisible realm of cyberspace.
Why are foreign hackers targeting private companies?
Private organizations harbor valuable intellectual property, technological research, and sensitive data that gleams like precious resources in the digital landscape. Access to this information provides economic and strategic advantages to rival nations, while businesses often serve as gateways into larger supply chains or government systems — each corporate network potentially offering passage to even greater treasures. Detailed analysis on why the private sector is targeted can be found via Microsoft’s Digital Defense Report.
What industries are most commonly targeted?
Certain sectors attract attention due to their strategic importance, like rare elements that nations seek to control. These often include technology companies, semiconductor manufacturers, energy providers, telecommunications firms, healthcare organizations, and companies involved in artificial intelligence or advanced research — each industry representing a different frontier in the race for technological supremacy.
How do nation-state hackers typically gain access to networks?
Attackers commonly employ tactics such as phishing emails, exploiting software vulnerabilities, credential theft, and supply chain compromises — each method serving as a different route into the digital territories they seek to explore. Once inside a network, they may attempt to move laterally across systems while remaining undetected for long periods, navigating these electronic landscapes with the stealth of skilled scouts in unfamiliar territory.
How can organizations defend against nation-state cyber threats?
While defending against highly sophisticated attackers presents challenges comparable to fortifying against well-equipped expeditionary forces, organizations can reduce risk by implementing robust cybersecurity practices. These include multi-factor authentication, network monitoring, patch management, employee security training, and adopting a zero-trust security model — each defense forming part of a comprehensive strategy to protect valuable digital territories from increasingly sophisticated intruders.